[sc name=”ad_1″]
SysAnalyzer is an open-source application that was designed to give malcode analysts an automated tool to quickly collect, compare, and report on the actions a binary took while running on the system.
A full installer for the application is available and can be downloaded here. The application supports windows 2000 – windows 10. Including x64 support.
The main components of SysAnalyzer work off of comparing snapshots of the system over a user-specified time interval. The reason a snapshot mechanism was used compared to a live logging implementation is to reduce the amount of data that analysts must wade through when conducting their analysis. By using a snapshot system, we can effectively present viewers with only the persistent changes found on the system since the application was first to run.
While this mechanism does help to eliminate a lot of the possible noise caused by other applications, or inconsequential runtime nuances, it also opens up the possibility for missing key data. Because of this SysAnalyzer also gives the analyst the option to include several forms of live logging into the analysis procedure.
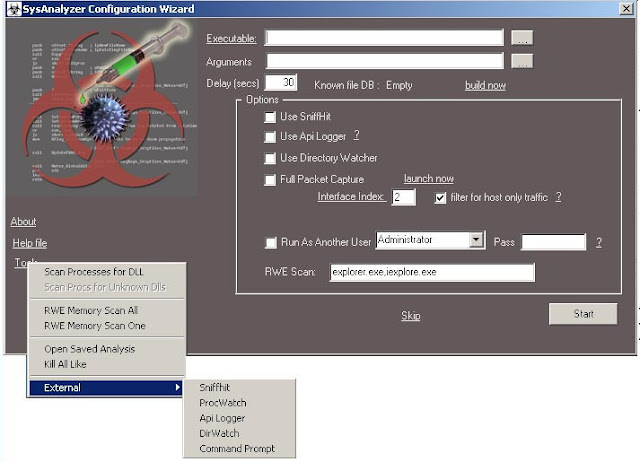
When first run, SysAnalyzer will present the user with the following configuration wizard:
The executable path textbox represents the file under analysis. It can be filled in either by
- Dragging and dropping the target executable on the SysAnalyzer desktop icon
- Specifying the executable on the command line
- Dragging and Dropping the target into the actual textbox
- Using the browse for file button next to the textbox
For files which must open in a viewer such as DOC or PDF files, specify the viewer app in the executable textbox, and the file itself in the arguments textbox.
there are handful of options available on the screen for optional live logging components such as full packet capture, API logger, and sniff hit. you can also run it as another user.
These options are saved to a configuration file and do not need to be entered each time. Note that users can also select the “Skip” link in order to proceed to the main interface where they can manually control the snapshot tools.
note that the API logger option is generally stable but not entirely so in every case. I generally reserved this option for when I need more information than a standard analysis provides.
Once these options are filled in and the user selects the “Start button” the options will be applied, a base snapshot of the system taken, and the executable launched.
[sc name=”ad-in-article”]


















Add Comment