CentOS which stands for Community Enterprise Operating System is one of the most widely used Linux distribution available for free. It powers many web servers...
Archive - October 2019
Hey Guys, In this video i show you How to Bypass Facebook Profile Picture Guard. Open the victim’s profile then right click on the page and click view page...
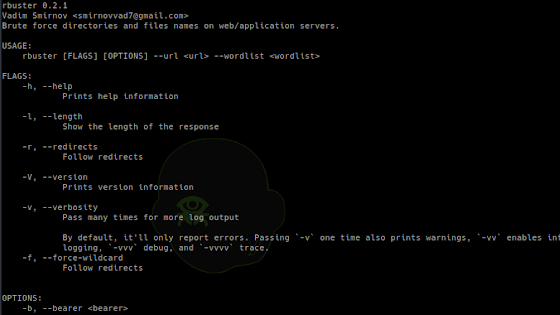
[sc name=”ad_1″] yet another dirbuster Common Command line options -a <user agent string> – specify a user agent string to send in the...
[sc name=”ad_1″] An XMLRPC brute forcer targeting WordPress written in Python 3. In the context of xmlrpc brute forcing, its faster than Hydra and...
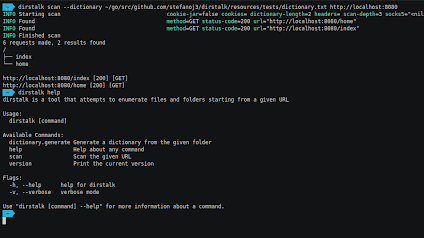
[sc name=”ad_1″] Dirstalk is a multi threaded application designed to brute force paths on web servers. The tool contains functionalities similar...
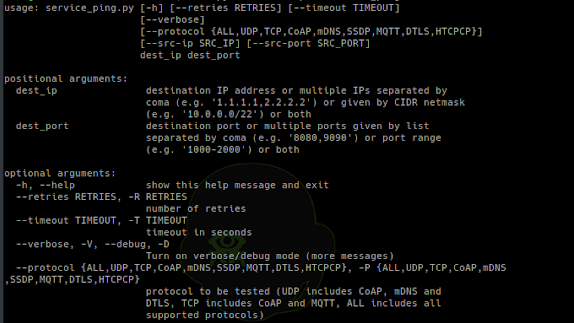
[sc name=”ad_1″] Set of tools for security testing of Internet of Things devices using protocols like: CoAP, DTLS, HTCPCP, mDNS, MQTT, SSDP...
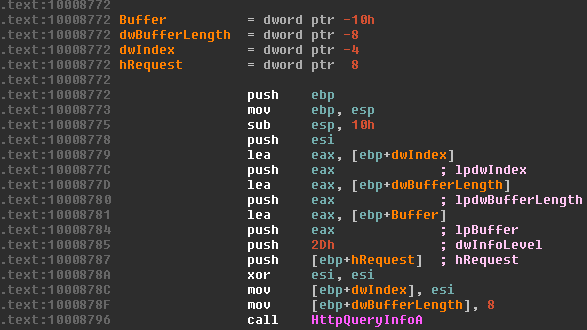
[sc name=”ad_1″] IDA PRO Auto-Renaming Plugin With Tagging Support Features 1. Auto-renaming dummy-named functions, which have one API call or jump...
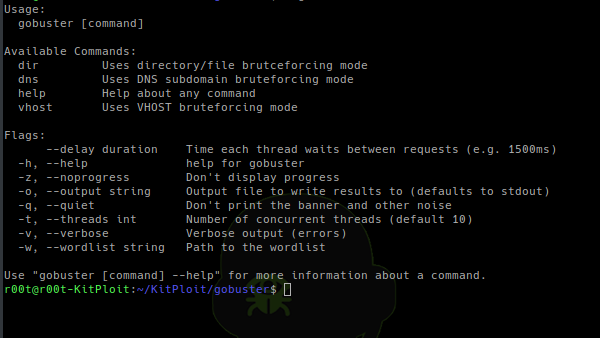
[sc name=”ad_1″] Gobuster is a tool used to brute-force: URIs (directories and files) in web sites. DNS subdomains (with wildcard support). Virtual...
[sc name=”ad_1″] RITA is an open source framework for network traffic analysis. The framework ingests Bro/Zeek Logs in TSV format, and currently...
[sc name=”ad_1″] by Gabriel Ryan (s0lst1c3)(gryan[at]specterops.io) EAPHammer is a toolkit for performing targeted evil twin attacks against WPA2...