frida-wshook is an analysis and instrumentation tool which uses frida.re to hook common functions often used by malicious script files which are run using WScript/CScript.
- .js (JScript)
- .vbs (VBScript)
- .wsf (WSFile) (Initial support/testing. – Does not support specific jobs)
- COM ProjIds
- DNS Requests
- Shell Commands
- Network Requests
Install & Setup
- Install Python 2.7
- Install the Frida python bindings using pip
pip install frida- Clone (or download) the frida-wshook repository.
Supported OS
frida-wshook has been tested on Windows 10 and Windows 7 and should work on any Windows 7 + environment. On x64 systems CScript is loaded from the C:WindowsSysWow64 directory.
It may work on WindowsXP, but I suspect that CScript may use the legacy API calls and would bypass the instrumentation.
Usage
The script supports a number of optional commandline arguments that allow you to control what APIs the scripting host can call.
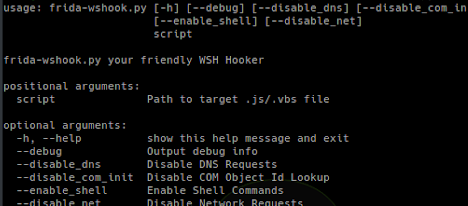
usage: frida-wshook.py [-h] [--debug] [--disable_dns] [--disable_com_init]
[--enable_shell] [--disable_net]
scriptfrida-wshook.py your friendly WSH Hooker
positional arguments:
script Path to target .js/.vbs file
optional arguments:
-h, --help show this help message and exit
--debug Output debug info
--disable_dns Disable DNS Requests
--disable_com_init Disable COM Object Id Lookup
--enable_shell Enable Shell Commands
--disable_net Disable Network Requests
Analyze a script with the default parameters:
python wshook.py bad.jsEnable verbose debugging:
python wshook.py --debug bad.jsEnable shell (execute) commands:
python frida-wshook.py --enable_shell bad.vbsDisable WSASend:
python frida-wshook.py --disable_net bad.vbsCheck what ProgIds the script uses:
python frida-wshook.py --disable_com_init bad.vbsHooked Functions
- ole32.dll
- Shell32.dll
- Ws2_32.dll
Known Issues
- Network responses are not captured
- Disabling Object Lookup can cause the script to only output the first ProgId…Malware QA can be lacking.
- WSF files with a specific job to target currently isn’t supported
TODO
- Change GetAddrInfoExW to use .replace instead of .attach
- Add additional tracing and hooks to cover more APIs
- Look at bypassing common anti-analysis techniques found in scripts (sleeps etc)
- Update and improve network request hooking (ie: currently it captures requests, but not responses)
Feedback / Help
Any questions, comments or requests you can find us on twitter: @seanmw or @herrcore



















Add Comment