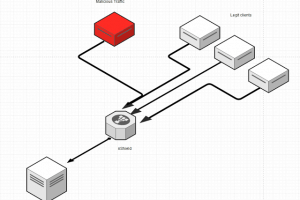
An Easy and Simple Anti-DDoS solution for VPS,Dedicated Servers and IoT devices based on iptables. Requirements Linux System with python, iptables Nginx (Will...
Search Results For - Configuration
sslh accepts connections on specified ports, and forwards them further based on tests performed on the first data packet sent by the remote client. Probes for...
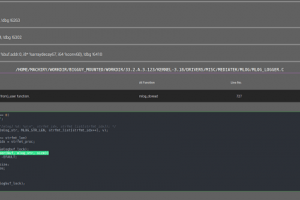
DR.CHECKER: A Soundy Vulnerability Detection Tool for Linux Kernel Drivers Tested on Ubuntu >= 14.04.5 LTS 1. Setup The implementation is based on LLVM...
A user-friendly Web interface to share an hashcat cracking box among multiple users with some pre-defined options. Outline This Web application can be used to...
DBC2 (DropboxC2) is a modular post-exploitation tool, composed of an agent running on the victim’s machine, a controler, running on any machine...
IP-Biter is an open source, easy to deploy, tracking framework that generate high configurables and uniques tracking images and links to embed in e-mails...
WSC2 is a PoC of using the WebSockets and a browser process to serve as a C2 communication channel between an agent, running on the target system, and a...
The GOSINT framework is a project used for collecting, processing, and exporting high quality indicators of compromise (IOCs). GOSINT allows a security analyst...
Newly uncovered vulnerabilities in a popular brand of indoor internet-connected cameras could be exploited by attackers in order to gain complete control of...
The Firefox sandboxing innovation confines the browser from the operating system in a way to block web attacks from using a vulnerability in the browser engine...