TrevorC2 is a client/server model for masking command and control through a normally browsable website. Detection becomes much harder as time intervals are...
Search Results For - Configuration
Comcast verified the statements in a tweet on its customer care account. The outage seems to have begun around 1 PM ET. Some users reached intermittent or slow...
CrunchRAT currently supports the following features: File upload File download Command execution It is currently single-threaded (only one task at a time), but...
Easily launch a new phishing site fully presented with SSL and capture credentials along with 2FA tokens using CredSniper. The API provides secure access to...
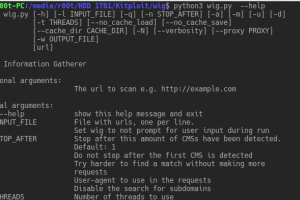
wig is a web application information gathering tool, which can identify numerous Content Management Systems and other administrative applications. The...
A robust Phishing Framework with a full featured CLI interface. The project was born out necessity through of years of engagements with tools that just didn’t...
Cybercriminals decided to use the Search Engine Optimization (SEO) to make their malicious links more widespread in the search results, allowing them to gain...
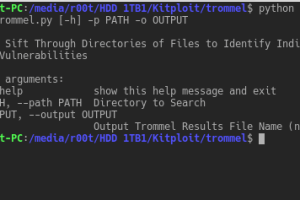
TROMMEL sifts through directories of files to identify indicators that may contain vulnerabilities. TROMMEL identifies the following indicators related to:...
FireEye’s Innovation and Custom Engineering (ICE) team released a tool called GoCrack that allows red teams to efficiently manage password cracking tasks...
We are excited to announce this major release of auditing tool Lynis. Several big changes have been made to core functions of Lynis. These changes are the next...