[sc name=”ad_1″]
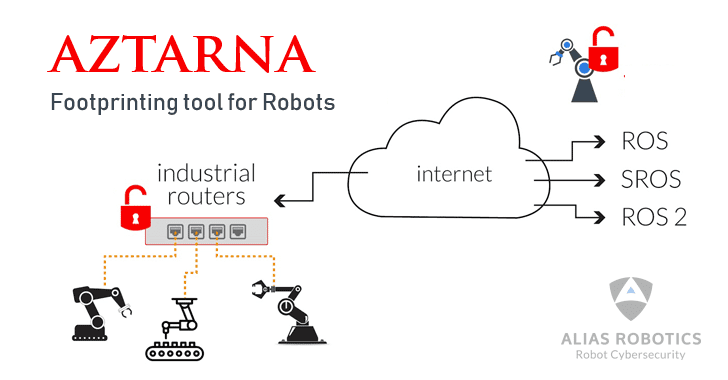
A team at a robot cybersecurity startup has released a free, open-source tool for information security professionals to help them easily ‘footprint’ and detect unprotected robots, not only connected to the Internet, but also to the industrial environments where they operate.
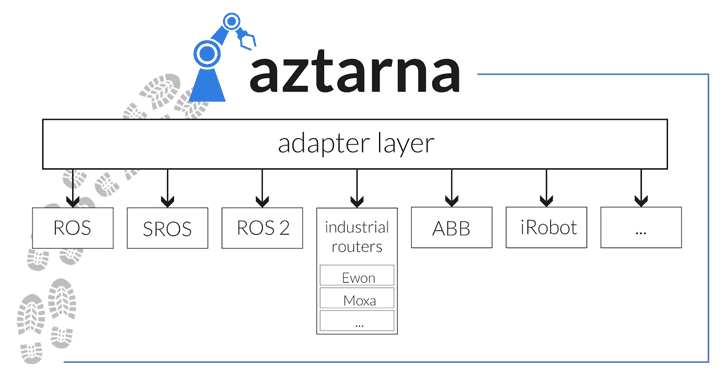
Dubbed “Aztarna,” the framework has been developed by Alias Robotics, a Spanish cybersecurity firm focused on robots and is capable of detecting vulnerable industrial routers and robots powered by ROS (Robot Operating System), SROS (Secure ROS) and other robot technologies.
Written in Python 3, Aztarna is basically a port scanning tool with a built-in database of fingerprints for industrial routers (including Westermo, Moxa, Sierra Wireless, and eWON), and robotic technologies and components, as well as patterns that power the tool to test those devices against various known vulnerabilities and security misconfigurations.
Researchers at Alias Robotics told The Hacker News that Aztarna has been designed to work in different work modes based upon different penetration testing scenarios. It can scan a list of given IP addresses, a network IP range, results from Shodan search engine and even the whole Internet in conjunction with other scanning tools like ZMap or masscan.
“Motivated by the lack of dedicated tooling for security research in the field of robotics, we have developed aztarna, a tool aimed to help in the detection and scan of robots and robot technologies (including software components) on a network,” the researchers said.
Using a quick scan with Aztarna, researchers detected almost 106 open ROS systems and 9,000 insecure industrial routers worldwide, a potential entry point for attackers to target vulnerable robots connected to the network, that can be accessed remotely using default credentials or even without requiring any authorization.
“Some the ROS instances found corresponded to empty systems or simulations, but a considerable proportion of real robots were identified. Including an array of research-oriented machines, but also a series of robots in industrial environments,” the researchers said.
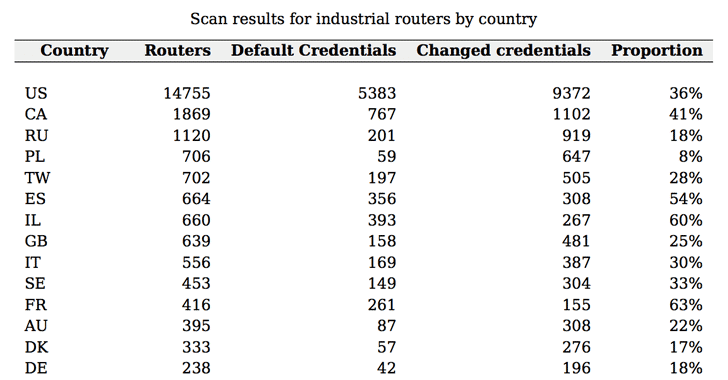
Most of the identified vulnerable routers (around 1,586) were found located in European countries, with France and Spain leading the ranking of misconfigured routers.
The highest amount of industrial routers were detected in North American countries with poor security settings in the 36 percent of the connected routers located in the United States and 41 percent in Canada.
According to the researchers, the open-source framework can easily be extended to receive more fingerprints and patterns with future releases and to support new software or hardware robot components, allowing researchers to determine the specific firmware version in robots and discover “third-party libraries used and their versions, e.g. robot middle-ware version, communication infrastructure, etc.”
Alias Robotics notified the owners of the bots about the vulnerable robots, but argued that the release of Aztarna is “a natural consequence of the general lack of concern among robot manufacturers towards security and cybersecurity.”
“It’s not only that they are very slow patching their flaws when we warn them. Many just don’t care and say: We know our robots have a set of reported vulnerabilities, but we leave security up to the end user,” the researchers wrote.
Alias Robotics researchers have also released a research paper [PDF] detailing Aztarna, how it can be reproduced and how it allows for future extensions. You can head on to the paper to know more about the open source footprinting tool for robots.



















Add Comment