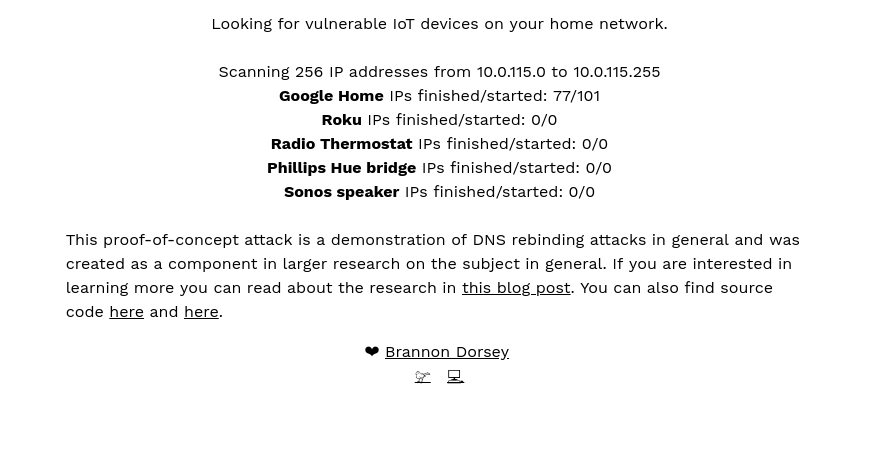
DNS Rebind Toolkit is a frontend JavaScript framework for developing DNS Rebinding exploits against vulnerable hosts and services on a local area network...
Sn1per Community Edition is an automated scanner that can be used during a penetration test to enumerate and scan for vulnerabilities. Sn1per Professional is Xero...
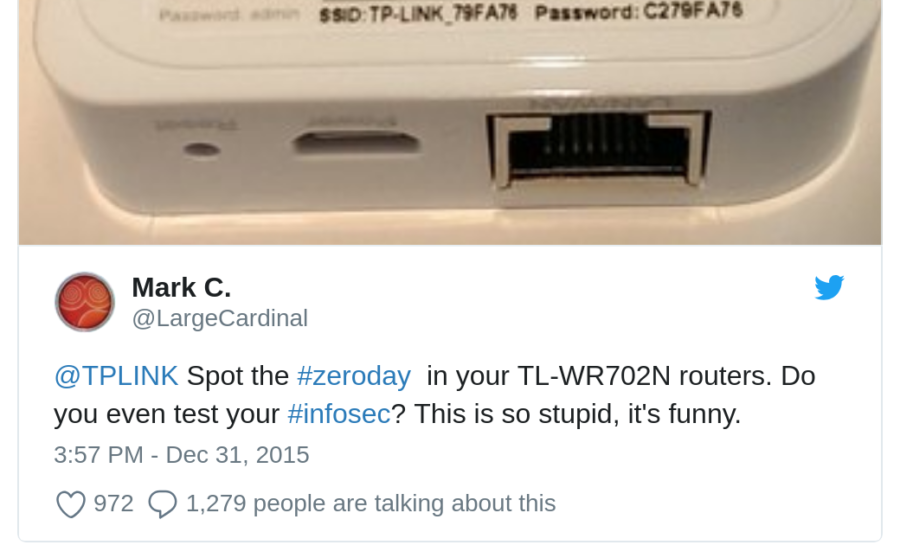
Python script for trying default passwords for some TP-Link Hotspots Inspired by Usage usage: scan.py [-h] [-p] Python script for trying default passwords for some TP...
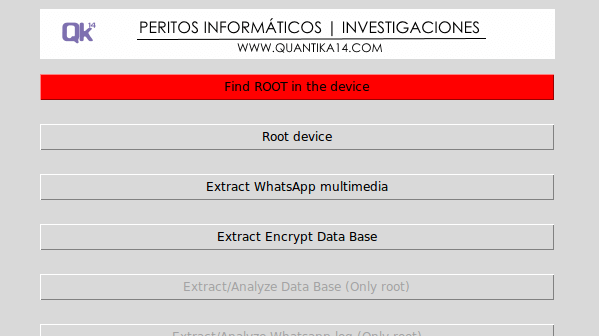
The Guasap Forensic implemented in Python under the GNU General Public License, for the extraction and analysis of files, data bases and logs for forensic WhatsApp. What...
Evil Remote Administration Tool (RAT) for macOS/OS X Features Emulate a terminal instance Simple extendable module system No bot dependencies (pure python) Undetected by...
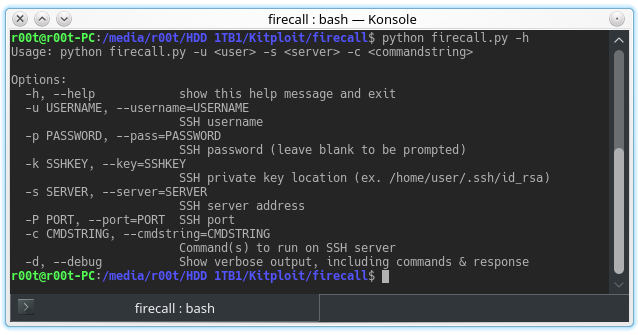
Automate SSH communication with firewalls, switches, etc. Description These scripts are designed to automate sending commands to a Cisco ASA firewall. The intended...
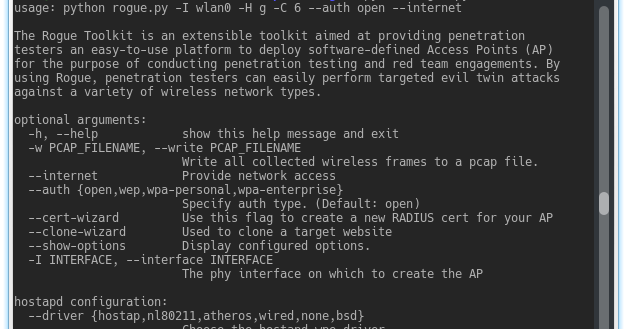
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for the...
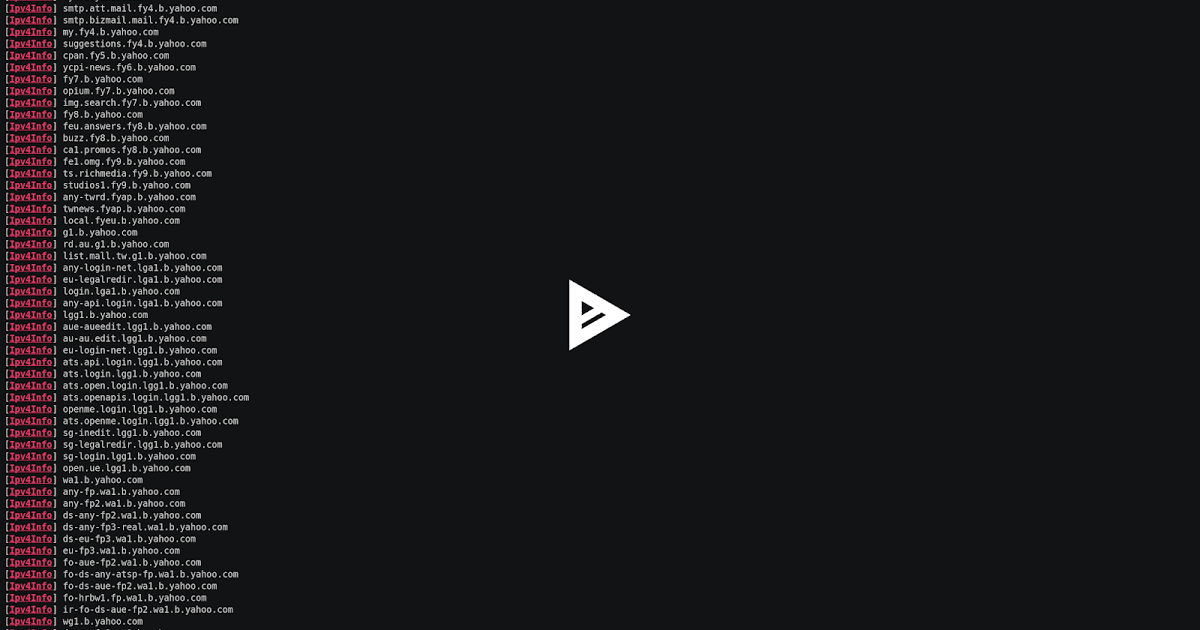
SubFinder is a subdomain discovery tool that discovers valid subdomains for websites by using passive online sources. It has a simple modular architecture and has been...
pspy is a command line tool designed to snoop on processes without need for root permissions. It allows you to see commands run by other users, cron jobs, etc. as they...
The aerospace industry, comprising aviation and space flight, generates trillions of dollars every year. Countries compete for the latest and greatest achievements in...