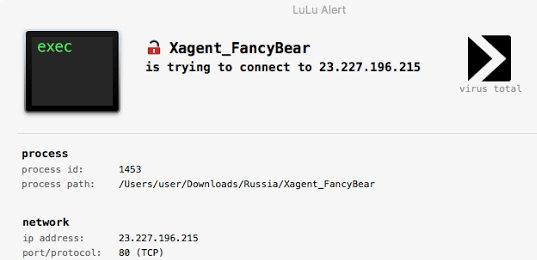
LuLu is the free open-source macOS firewall that aims to block unauthorized (outgoing) network traffic, unless explicitly approved by the user:
Full details and usage instructions can be found here.
It’s also important to understand LuLu’s limitations! Some of these will be addressed as the software matures, while others are design decisions (mostly with the goal of keeping things simple).
Network Monitoring
By design, LuLu only monitors for outgoing network connections. Apple’s built in firewall does a great job blocking unauthorized incoming connections.
Rules
Currently, LuLu only supports rules at the ‘process level’, meaning a process (or application) is either allowed to connect to the network or not. As is the case with other firewalls, this also means that if a legitimate (allowed) process is abused by malicious code to perform network actions, this will be allowed.
Single User
For now, LuLu can only be installed for a single user. Future versions will likely allow it to be installed by multiple users on the same system.
Self-Defense
Legitimate attackers/security professionals know that any security tool can be trivially bypassed if specifically targeted – even if the tool employs advanced self-defense mechanisms. Such self-defense mechanisms are often complex to implement and in the end, almost always futile. As such, by design LuLu (currently) implements few self-defense mechanisms. For example, an attacker could enumerate all running processes to find the LuLu component responsible for displaying alerts and terminate it (via a sigkill).
Limited Features
As LuLu is currently in alpha, certain features have not (yet) been implemented. For example, alert windows shown by LuLu currently only contain the ip address of the remote endpoint, not the URL. Stay tuned for updates that address these short-comings!
To Build
LuLu should build cleanly in Xcode (though you will have to remove code signing constraints, or replace with your own Apple developer/kernel code signing certificate).
To Install
For now, LuLu must be installed via the command-line. Build LuLu or download the pre-built binaries/components from the Releases page, then execute the configuration script (configure.sh) with the -install flag, as root:
//install
$ sudo configure.sh -install



















Add Comment