[sc name=”ad_1″]
Cybersecurity researchers today disclosed details of two newly identified Magecart attacks targeting online shoppers of bedding retailers MyPillow and Amerisleep.
Magecart is an umbrella term researchers gave to at least 11 different hacking groups that are specialized in implanting malware code on e-commerce websites with an intent to steal payment card details of their customers silently.
Magecart made headlines last year after attackers conducted several high-profile cyber attacks against major international companies including British Airways, Ticketmaster, and Newegg.
Magecart hackers use a digital payment card skimmer, a few lines of malicious Javascript code they insert into the checkout page of hacked websites and designed to captured payment information of customers in real time and then send it to a remote attacker-controlled server.
Earlier this year, Magecart attackers also compromised nearly 277 e-commerce websites in a supply-chain attack by inserting its skimming code into a popular third-party JavaScript library from Adverline.
That widely spread cyber attack eventually targeted all customers who made online purchases on hundreds of European e-commerce sites that were serving a modified Adverline script.
MageCart Hackers Target Bedding Retailers MyPillow and Amerisleep
In a new report RiskIQ shared with The Hacker News before its publication, researchers revealed two new Magecart-related breaches that compromised online bedding retailers MyPillow and Amerisleep and stole payment information of their customers.
Just like previous attacks, after finding a way to get a foothold on the targeted websites, the Magecart hackers implanted digital skimming code on both websites and managed to skim payment cards of their customers during online transactions.
MyPillow was breached by the Magecart attackers in October last year, wherein attackers inserted malicious skimming script on the site that was hosted on a look-alike domain (also known as typosquatting) with an SSL certificate from LetsEncrypt.
“The last time we observed this skimmer active on the MyPillow website was November 19th. Since then, we have not observed newly registered domains for attacks on MyPillow,” the researchers say.
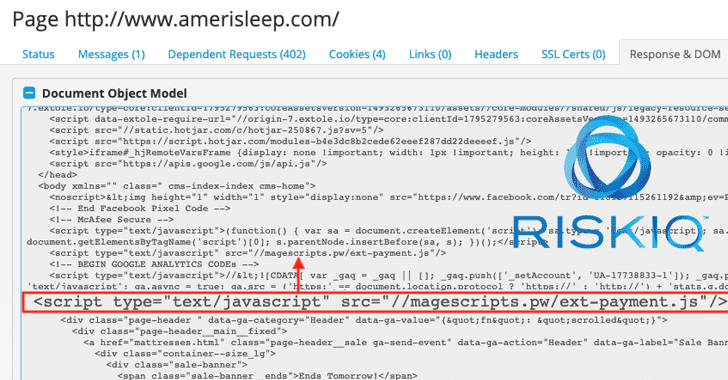
Another mattress company, Amerisleep, was targeted by Magecart attackers several times in 2017 to skim its customers’ cards during online transactions, but again became a victim of the attack in December 2018, when Magecart attackers hosted malicious code containing skimmers on a Github account.
However, the most recent attack against the company was observed in January this year, when the attackers decided to move some conditional checks so that their skimmers got injected only on payment pages, instead of every page.
“While the skimmer domain has been taken offline, the injection is still live on the website as of this publishing,” RisKIQ says. “Attempts to inform Amerisleep through their support desk and directly via email has gone unanswered.”

What’s more? Despite being attacked for several months, neither MyPillow nor Amerisleep issued any alert or official statement warning their customers about the Magecart attack that may have been compromised their payment details.
Since attackers usually exploit known vulnerabilities in online e-commerce software, websites administrators are highly advised to follow standard best practices, such as applying latest updates and patches, limiting privileges for critical systems and hardening web servers.
Online shoppers should also regularly review their credit card and bank statements for unfamiliar activities. No matter how small unauthorized transaction you notice, affected users should always report it to their financial institutions immediately.




















Add Comment