[sc name=”ad_1″]
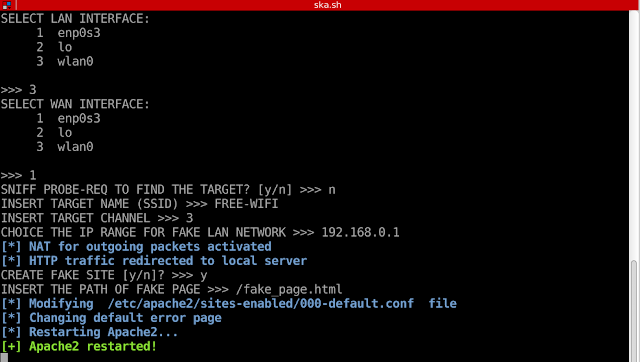
SKA allows you to implement a very simple and fast karma attack.
You can sniff probe requests to choice the fake AP name or, if you want, you could insert manually the name of the AP (evil twin attack).
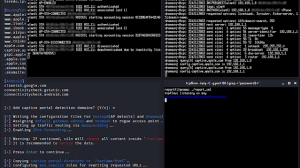
When the target has connected to your WLAN you could active the HTTP redirection and perform a MITM attack.
Details
The script implements these steps:
- selection of NICs for the attack (one for LAN and one for WAN)
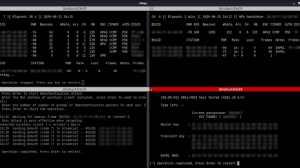
- capture of probe-requests to choice the fake AP name (tcpdump)
- activation of fake AP (hostapd and dnsmasq)
- the new AP has a DHCP server which provides a valide IP to the target and prevents possible alerts on the victim devices
- activation of HTTP redirection (iptables)
- only HTTP requests are redirect to fake site, while the HTTPS traffic continues to route normally
- activation of Apache server for hosting the phising site
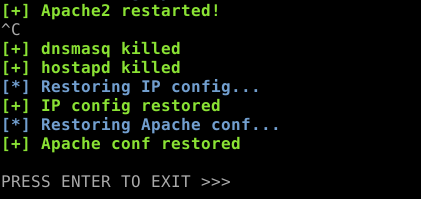
- at the end of the attack the script cleans all changes and restores Apache configuration
Screenshots
Press CTRL-C to kill all processes and restore the configuration files.
FAQ
SKA alerts you if there are some problems with NetworkManager demon or Apache configuration file. Anyway you could find the answers to your problems in the links below:
- resolve Network Manager conflict 1
section: “Resolve airmon-ng and Network Manager Conflict” - resolve Network Manager conflict 2
- disable dnsmasq
In summary
- Disable DNS line in your NetworkManager configuration file (look into /etc/NetworkManager/):
#dns=dnsmasq - Insert the MAC of your wireless adapter between the unmanaged devices to allow hostapd works properly:
unmanaged-devices=mac:XX:XX:XX:XX:XX:XX
[sc name=”ad-in-article”]



















Add Comment