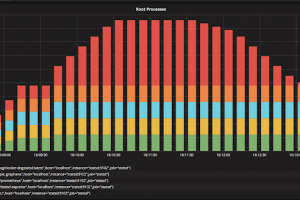
The Port Scan Attack Detector psad is a lightweight system daemon written in is designed to work with Linux iptables/ip6tables/firewalld firewalling code to...
Search Results For - Iptables
[sc name=”ad_1″] nginx Docker image secure by default. Avoid the hassle of following security best practices each time you need a web server or...
[sc name=”ad_1″] DNX Firewall is an optimized/high performance collection of applications or services to convert a standard linux system into a...
[sc name=”ad_1″] What is “Kill Chain”? From Wikipedia: The term kill chain was originally used as a military concept related to the structure of an...
[sc name=”ad_1″] cnitch (snitch or container snitch) is a simple framework and command line tool for monitoring Docker containers to identify any...
[sc name=”ad_1″] Hardened Debian GNU/Linux and CentOS 8 distro auditing. The main test environment is in debian GNU/Linux 9/10 and CentOS 8, and...
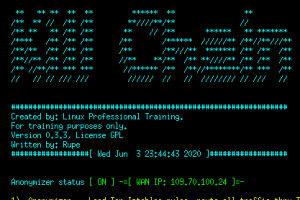
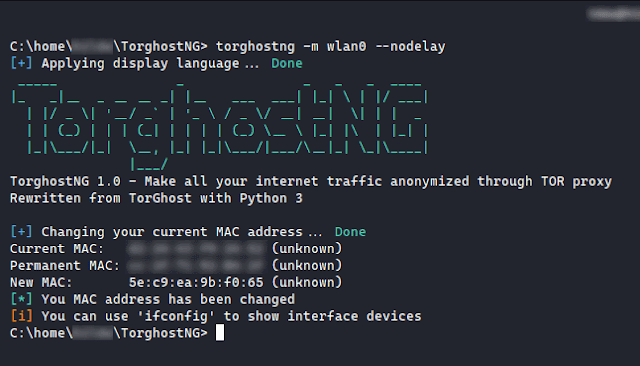
[sc name=”ad_1″] TorghostNG is a tool that make all your internet traffic anonymized through Tor network. Rewritten from TorGhost with Python 3...
[sc name=”ad_1″] SKA allows you to implement a very simple and fast karma attack. You can sniff probe requests to choice the fake AP name or, if...
[sc name=”ad_1″] Dolos Cloak is a python script designed to help network penetration testers and red teamers bypass 802.1x solutions by using an...
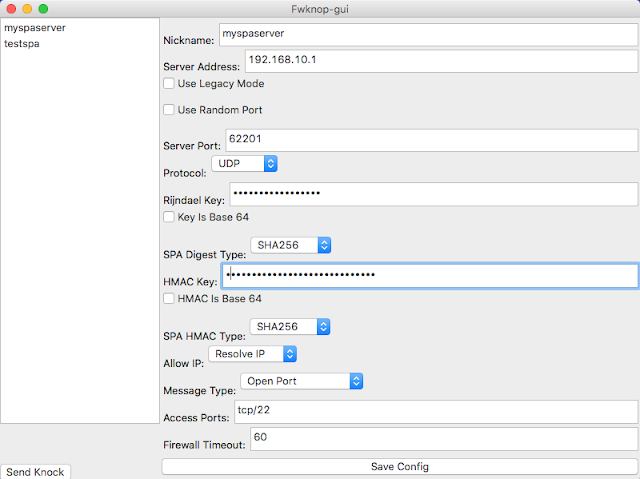
[sc name=”ad_1″] fwknop implements an authorization scheme known as Single Packet Authorization (SPA) for strong service concealment. SPA requires...