TrevorC2 is a client/server model for masking command and control through a normally browsable website. Detection becomes much harder as time intervals are different and does not use POST requests for data exfil.
There are two components to TrevorC2 – the client and the server. The client can be configured to be used with anything. In this example it’s coded in Python but can easily be ported to C#, PowerShell, or whatever you want. Currently the trevorc2_client.py supports Windows, MacOS, and Linux. You can always byte compile the Windows one to get an executable, but preference would be to use Windows without having to drop an executable as a stager.
The way that the server works is by tucking away a parameter thats right before the parameter. This is completely configurable, and it’s recommended you configure everything to be unique in order to evade detection. Here is the workflow:
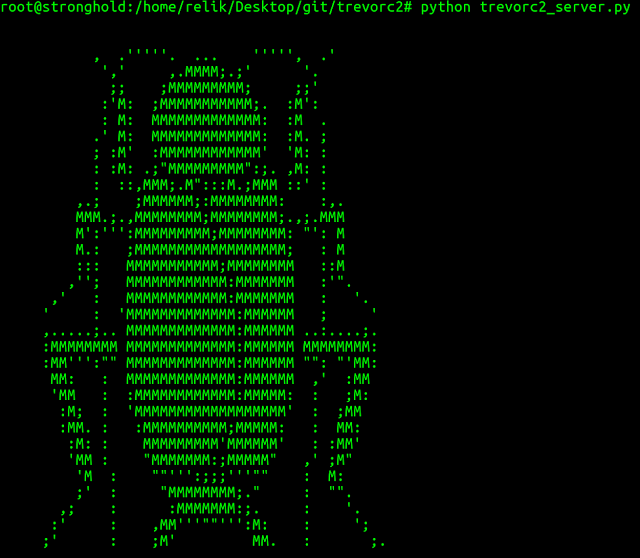
1. trevor2_server.py - edit the file first, and customize, what website you want to clone, etc. The server will clone a website of your choosing and stand up a server. This server is browsable by anyone and looks like a legitimate website. Contained within the source is parameter that (again is configurable), which contains the instructions for the client. Once a client connects, it searches for that parameter, then uses it to execute commands.
2. trevor2_client.py - all you need in any configurable option is the ability to call out to a website, parse some basic data, and then execute a command and then put the results in a base64 encoded query string parameter to the site. That's it, not hard. Installation
pip install -r requirements.txtUsage
First edit the trevor2_server.py – change the configuration options and site to clone.
python trevor2_server.pyNext, edit the trevor2_client.py – change the configuration and system you want it to communicate back to.
python trevor2_client.py

















Add Comment