Hacking requires a lot of brainstorming since you need a robust machine that will not lag or run out of resources during working. Hacking involves DDOS a...
Search Results For - Configuration
Hardentools is a collection of simple utilities designed to disable a number of “features” exposed by operating systems (Microsoft Windows, for now), and...
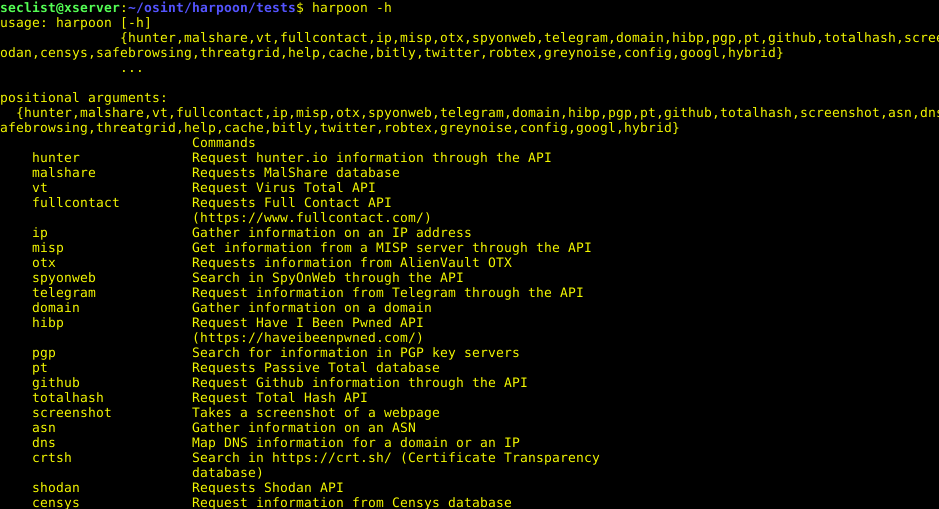
OSINT tool, CLI Tool For Open Source And Threat Intelligence Install You can simply pip install the tool: pip3 install git+ --process-dependency-links...
bettercap is the Swiss army knife for network attacks and monitoring. How to Install A precompiled version is available for each release, alternatively you can...
MSDAT (Microsoft SQL Database Attacking Tool) is an open source penetration testing tool that tests the security of Microsoft SQL Databases remotely. Usage...
GlobaLeaks is an open-source, free software intended to enable secure and anonymous whistleblowing initiatives developed by the Hermes Center for Transparency...
Script to steal passwords from SSH. Install git clone cd sshLooter Configuration Edit the script on install.sh, and add your telegram bot api, and your userid...
[sc name=”ad_1″] Hacking a Wi-Fi network using Kali Linux needs a wireless card that support monitor mode and packet injection. Not all wireless...
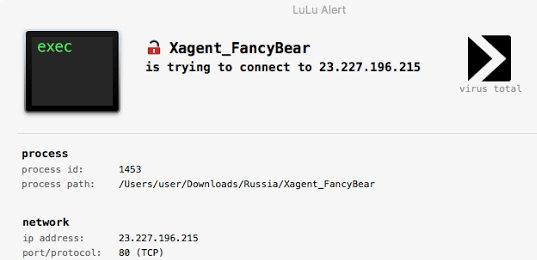
LuLu is the free open-source macOS firewall that aims to block unauthorized (outgoing) network traffic, unless explicitly approved by the user: Full details...
ElasticIntel is serverless, low cost, threat intel aggregation for enterprise or personal use, backed by ElasticSearch. It is an alternative to expensive...