Hindsight is a free tool for analyzing web artifacts. It started with the browsing history of the Google Chrome web browser and has expanded to support other Chromium...
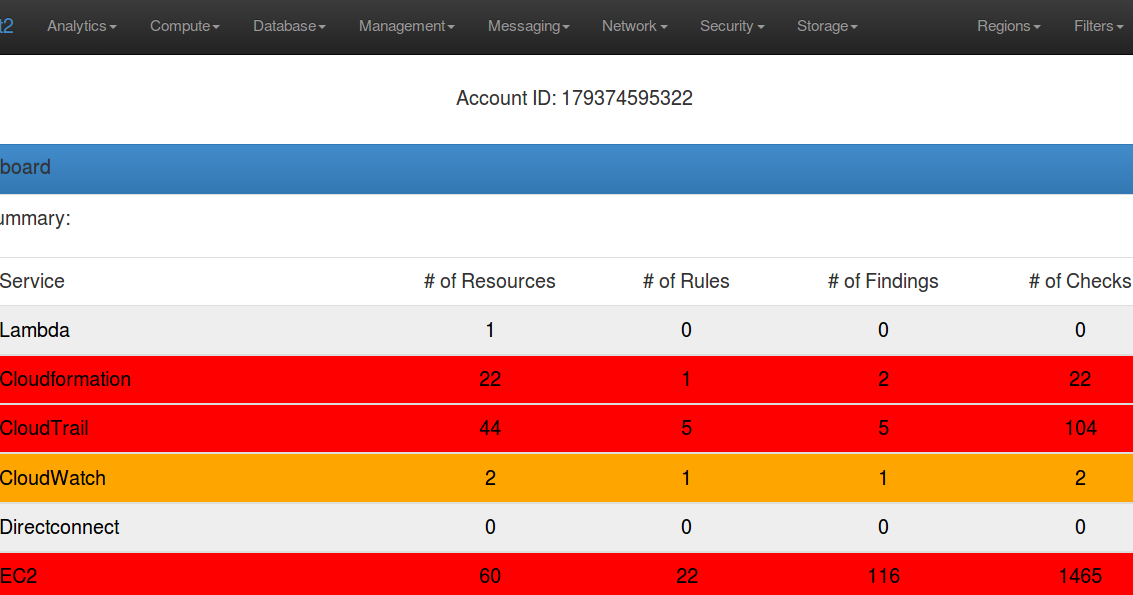
Scout2 is a security tool that lets AWS administrators assess their environment’s security posture. Using the AWS API, Scout2 gathers configuration data for manual...
A powerful tool for managing networks and troubleshoot network problems! Features Network Interface – Information, Configure IP-Scanner Port-Scanner Ping...
Seeker utilizes HTML5, Javascript, JQuery and PHP to grab Device Information and GeoLocation with High Accuracy. Seeker Hosts a fake website on Apache Server and uses...
Domain Hijacking is a well-known security issue that can be carried in many different ways. In addition to social engineering or unauthorized access to the domain...
Security Monkey monitors your AWS and GCP accounts for policy changes and alerts on insecure configurations. Support is available for OpenStack public and private clouds...
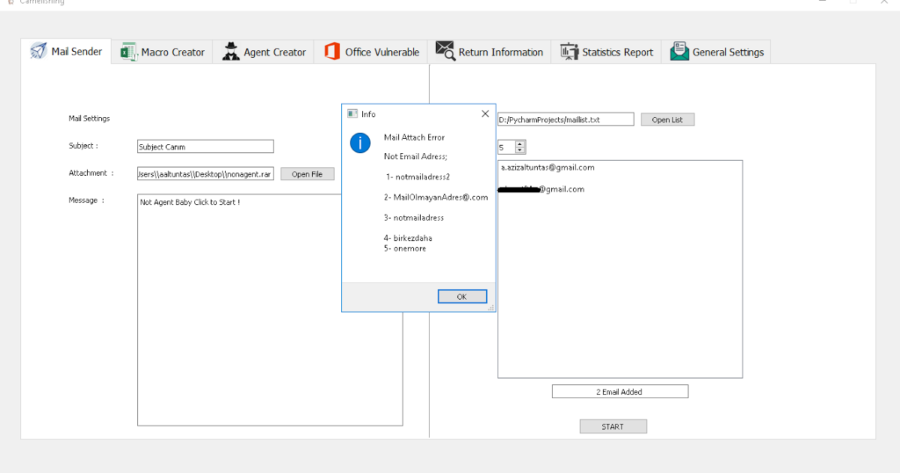
Camelishing Social Engineering Tool Features Bulk email sending Basic Python Agent Creator Office Excel Macro Creator DDE Excel Creator(or Custom Payload) Return...
Weevely is a web shell designed for post-exploitation purposes that can be extended over the network at runtime. Upload weevely PHP agent to a target web server to get...
[sc name=”ad_1″] A theme is a collection of background image, window color and with theme can be given according to the picture as you wish. images and...
In computing, load balancing improves the distribution of workloads across multiple computing resources, such as computers, a computer cluster, network links, central...