[sc name=”ad_1″] Detect compliance and security violations across Infrastructure as Code to mitigate risk before provisioning cloud native...
Search Results For - Infrastructure
[sc name=”ad_1″] A multiprocessing approach to auditing Active Directory passwords using Python. About Lil Pwny Lil Pwny is a Python application to...
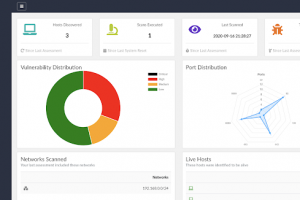
[sc name=”ad_1″] NERVE is a vulnerability scanner tailored to find low-hanging fruit level vulnerabilities, in specific application configurations...
[sc name=”ad_1″] Bug Bounty Recon (bbrecon) is a free Recon-as-a-Service for bug bounty hunters and security researchers. The API aims to provide a...
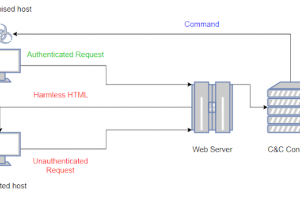
[sc name=”ad_1″] LOLBITS is a C2 framework that uses Microsoft’s Background Intelligent Transfer Service (BITS) to establish the...
[sc name=”ad_1″] Did you ever wonder how you can move laterally through internal networks? or interact with remote machines without alerting EDRs...
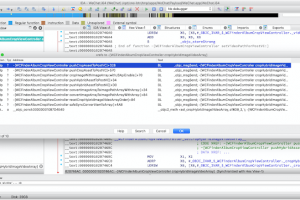
[sc name=”ad_1″] iblessing iblessing is an iOS security exploiting toolkit, it mainly includes application information collection, static analysis...
[sc name=”ad_1″] Yeti is a platform meant to organize observables, indicators of compromise, TTPs, and knowledge on threats in a single, unified...
[sc name=”ad_1″] Cloud Security Operations What is Cloud Sniper? Cloud Sniper is a platform designed to manage Security Operations in cloud...
[sc name=”ad_1″] A proof of concept crypto virus to spread user awareness about attacks and implications of ransomwares. Phirautee is written...