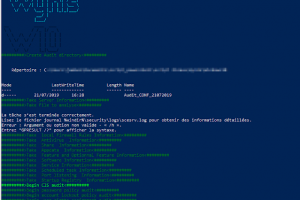
[sc name=”ad_1″] Just a powershell scripts for auditing security with CIS BEST Practices Windows 10 and Window Server 2016 You just need to run the...
Search Results For - Configuration
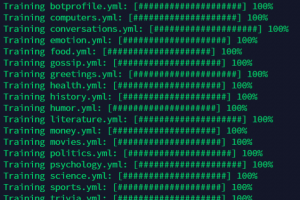
[sc name=”ad_1″] Aura is a static analysis framework developed as a response to the ever-increasing threat of malicious packages and vulnerable...
[sc name=”ad_1″] A sharpen version of CrackMapExec. This tool is made to simplify penetration testing of networks and to create a swiss army knife...
[sc name=”ad_1″] Automated Web Assets Enumeration & Scanning Instructions for running Create an account on Zulip Navigate to...
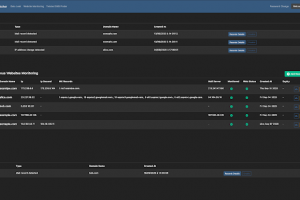
[sc name=”ad_1″] Watcher is a Django & React JS automated platform for discovering new potentially cybersecurity threats targeting your...
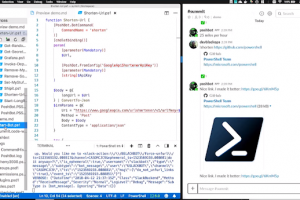
[sc name=”ad_1″] PoshBot is a chat bot written in PowerShell. It makes extensive use of classes introduced in PowerShell 5.0. PowerShell modules...
[sc name=”ad_1″] GUSTAVE is a fuzzing platform for embedded OS kernels. It is based on QEMU and AFL (and all of its forkserver siblings). It allows...
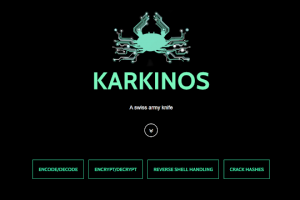
[sc name=”ad_1″] Karkinos is a light-weight ‘Swiss Army Knife’ for penetration testing and/or hacking CTF’s. Currently, Karkinos...
[sc name=”ad_1″] enum4linux-ng.py is a rewrite of Mark Lowe’s (former Portcullis Labs now Cisco CX Security Labs) enum4linux.pl, a tool for...
[sc name=”ad_1″] A small contribution to community 🙂 We use all these tools in security assessments and in our vulnerability monitoring service...