Author: David Hamilton The banking system is inefficient in its current state as it requires the use of multiple third-party verifications and transferring...
Search Results For - Check
Often during the penetration test engagement the security analyst faces the problem of identifying privilege escalation attack vectors on tested Linux...
This Kali release is the first to include the Linux 4.15 kernel, which includes the x86 and x64 fixes for the much-hyped Spectre and Meltdown vulnerabilities...
Interview: Aragon’s Luis Cuende on Blockchain Governance & Digital Jurisdictions Author: Bennett Garner Bennett Garner: You’ve said “humans enforce...
M$ Windows Hacking Pack =========== Tools here are from different sources. The repo is generally licensed with WTFPL, but some content may be not (eg...
Red Team Arsenal is a web/network security scanner which has the capability to scan all company’s online facing assets and provide an holistic security view of...
Hey Guys, In this video i show you how to perform Wi-Fi deauthentication attack on any Wi-Fi Network. Wi-Fi deauthentication attack is a type of denial-of...
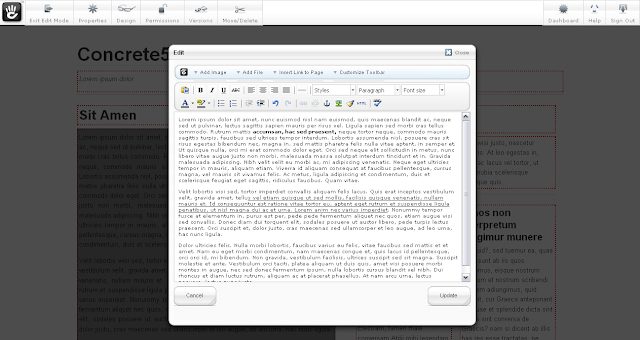
Vulnerability scanner and information gatherer for the Concrete5 CMS. Is a little out of date presently pending a refactor. concrete5 is an open-source content...
CHAOS allow generate payloads and control remote Windows systems. Features Reverse Shell Download File Upload File Screenshot ? Keylogger ? Persistence Open...
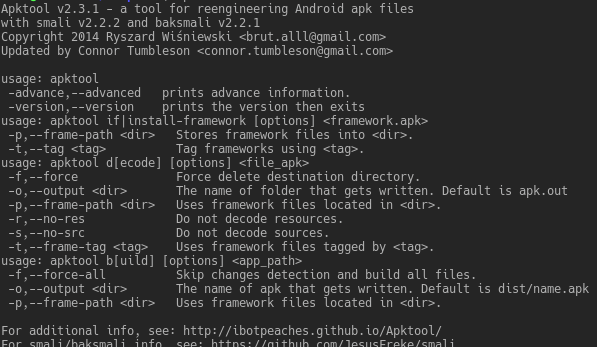
A tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some...