[sc name=”ad_1″] Google has recently released the first beta version of Android Q, the next upcoming version of Google’s popular mobile operating...
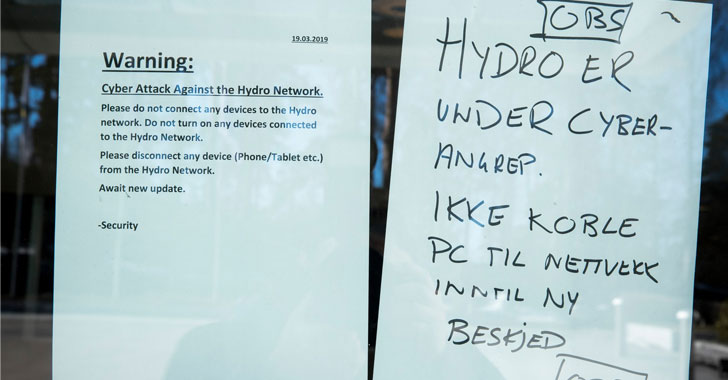
[sc name=”ad_1″] Photo by Terje Pedersen / NTB scanpix One of the world’s largest producers of aluminum has been forced to shut down several of its...
[sc name=”ad_1″] Libssh2, a popular open source client-side C library implementing the SSHv2 protocol, has released the latest version of its software to...
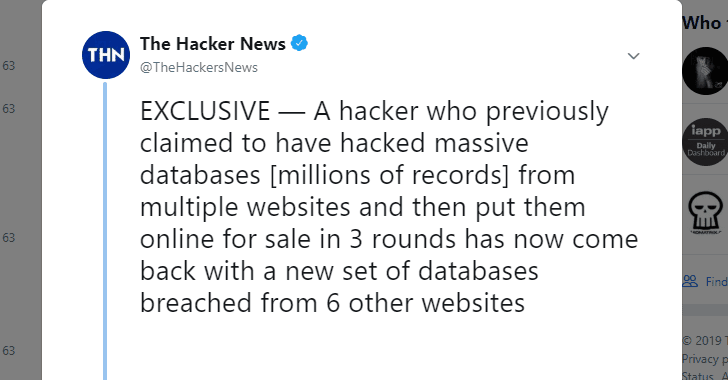
[sc name=”ad_1″] A hacker who was selling details of nearly 890 million online accounts stolen from 32 popular websites in three separate rounds has now put...
[sc name=”ad_1″] Various cyber criminal groups and individual hackers are still exploiting a recently patched critical code execution vulnerability in...
[sc name=”ad_1″] If you are a Counter-Strike gamer, then beware, because 39% of all existing Counter-Strike 1.6 game servers available online are malicious...
[sc name=”ad_1″] If for some reason your WordPress-based website has not yet been automatically updated to the latest version 5.1.1, it’s highly...
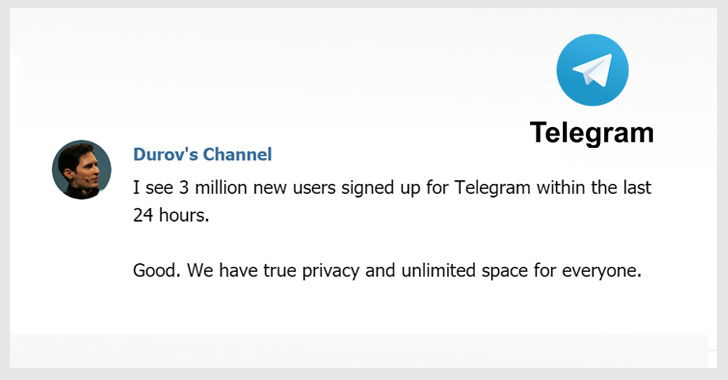
[sc name=”ad_1″] WhatsApp, Facebook, and Instagram faced a widespread outage yesterday with users from around the world reporting issues with sending...
[sc name=”ad_1″] One of the most important software companies NGINX, which is also behind the very popular open-source web server of the same name, is being...
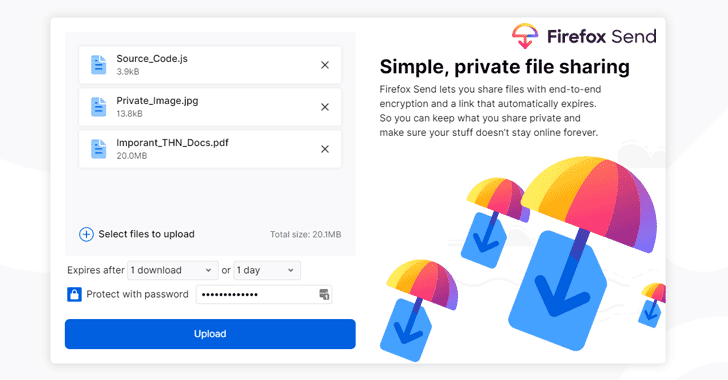
[sc name=”ad_1″] Mozilla has made it easy for you to share large files securely and privately with whomever you want, eliminating the need to depend upon...