LFiFreak is a tool for exploiting local file inclusions using PHP Input, PHP Filter and Data URI methods. Features Works with Windows, Linux and OS X Includes bind and...
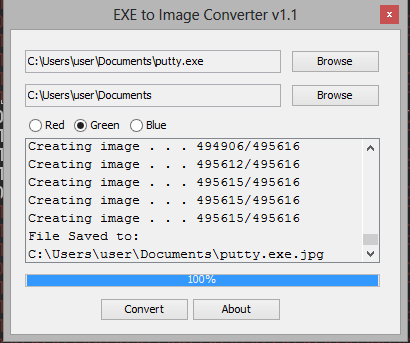
A simple utility to convert EXE files to PNG images and vice versa.
Putty.exe converted to an image.
Download Exe2Image
Tails is a live system that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously and circumvent censorship almost anywhere you go...
Do you know—United States Government has banned federal agencies from using Kaspersky antivirus software over spying fear? Though there’s no solid evidence yet...
If you are an iPhone user and use Uber app, you would be surprised to know that widely popular ride-hailing app can record your screen secretly. Security researcher Will...
A severe programming error has been discovered in Apple’s latest macOS High Sierra 10.13 that exposes passwords of encrypted Apple File System (APFS) volumes in...
Hey Guys, In this video i show you how to generate shellcodes and Backdoors using ShellSploit Framework and Kali Linux 2017.2. ShellSploit: Shellsploit let’s you...
Hey Guys, In this video i show you a great tool called Yuki Chan. The Yuki Chan is an Automated Penetration Testing tool this tool will auditing all standard security...
Hey Guys, In this video i show you how to use PasteJacking to hack any operating system using PasteZort and Kali Linux 2017.1. PasteZort: Installation and Usage: git...
Hey Guys, In this video i show you a great Web Application Security Scanner called Spaghetti. Spaghetti is a web application security scanner tool. It is designed to...