Hey Guys, In this video i show you create your own private search engine using Searx. SearX: Installer Script: Searx is a free metasearch engine, available under the GNU...
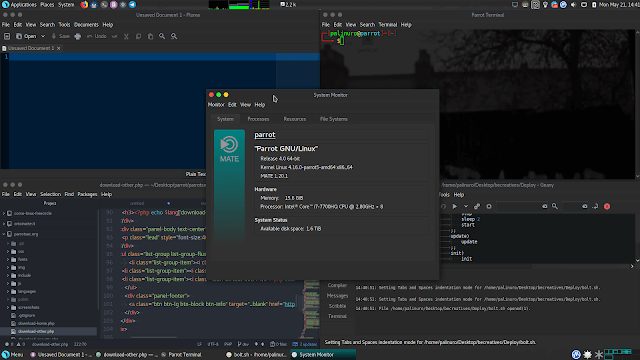
Parrot 4.0 is now available for download. The development process of this version required a lot of time, and many important updates make this release an important...
Hey Guys, To join HackTheBox, you will need an invite code, In this video i show you how to get an invite code for HackTheBox. Hack The Box is an online platform...
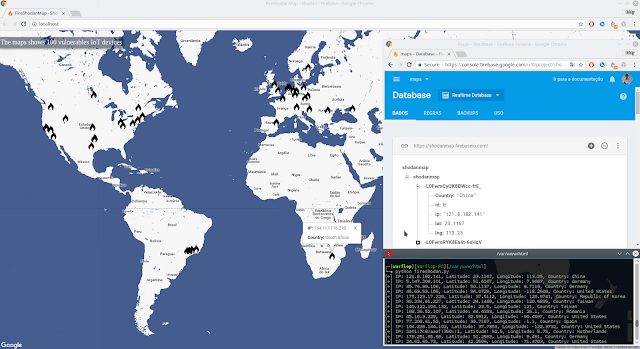
FireShodanMap is a Realtime map that integrates Firebase and Shodan. A search is carried out using Shodan searching vulnerable devices and they are showed on the map for...
The goal of this volatility plugin is to extract a screenshot of all open X windows from a memory dump. Overview The plugin first dumps the X server memory mappings...
A tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some modifications...
Phantom-Evasion is an interactive antivirus evasion tool written in python capable to generate (almost) FUD executable even with the most common 32 bit msfvenom payload...
Author: David Hamilton The banking system is inefficient in its current state as it requires the use of multiple third-party verifications and transferring services in...
[sc name=”ad_1″] Most of us are very curious to know a method to send spoofed emails to our friends and family for fun. But the question is, is it possible...
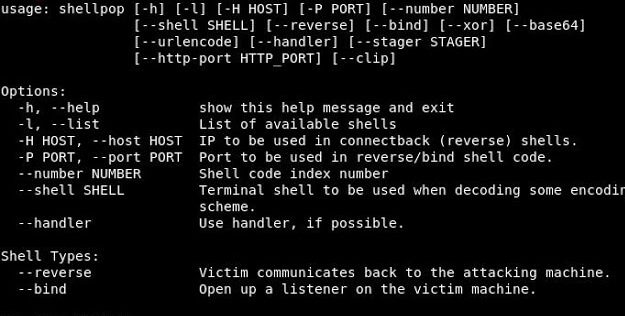
Pop shells like a master Shell pop is all about popping shells. With this tool you can generate easy and sofisticated reverse or bind shell commands to help you during...