[sc name=”ad_1″]
Sherlock, a powerful command line tool provided by Sherlock Project, can be used to find usernames across many social networks. It requires Python 3.6 or higher and works on MacOS, Linux and Windows.
Installation
NOTE: Python 3.6 or higher is required.
# clone the repo
$ git clone https://github.com/sherlock-project/sherlock.git
# change the working directory to sherlock
$ cd sherlock
# install python3 and python3-pip if they are not installed
# install the requirements
$ python3 -m pip install -r requirements.txt
Usage
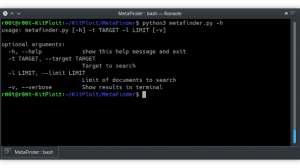
$ python3 sherlock --help
usage: sherlock [-h] [--version] [--verbose] [--rank]
[--folderoutput FOLDEROUTPUT] [--output OUTPUT] [--tor]
[--unique-tor] [--csv] [--site SITE_NAME] [--proxy PROXY_URL]
[--json JSON_FILE] [--timeout TIMEOUT] [--print-found]
[--no-color] [--browse]
USERNAMES [USERNAMES ...]
Sherlock: Find Usernames Across Social Networks (Version 0.12.2)
positional arguments:
USERNAMES One or more usernames to check with social networks.
optional arguments:
-h, --help show this help message and exit
--version Display version information and dependencies.
--verbose, -v, -d, --debug
Display extra debugging information and metrics.
--rank, -r Present websites ordered by their Alexa.com global
rank in popularity.
--folderoutput FOLDEROUTPUT, -fo FOLDEROUTPUT
If using multiple usernames, the output of the results
will be saved to this folder.
--output OUTPUT, -o OUTPUT
If using single username, the output of the result
will be saved to this file.
--tor, -t Make requests over Tor; increases runtime; requires
Tor to be installed and in system path.
--unique-tor, -u Make requests over Tor with new Tor circuit after each
request; increases runtime; requires Tor to be
installed and in system path.
--csv Create Comma-Separated Values (CSV) File.
--site SITE_NAME Limit analysis to just the listed sites. Add multiple
options to specify more than one site.
--proxy PROXY_URL, -p PROXY_URL
Make requests over a proxy. e.g.
socks5://127.0.0.1:1080
--json JSON_FILE, -j JSON_FILE
Load data from a JSON file or an online, valid, JSON
file.
--timeout TIMEOUT Time (in seconds) to wait for response to requests.
Default timeout of 60.0s.A longer timeout will be more
likely to get results from slow sites.On the other
hand, this may cause a long delay to gather all
results.
--print-found Do not output sites where the username was not found.
--no-color Don't color terminal output
--browse, -b Browse to all results on default bowser.
To search for only one user:
python3 sherlock user123
To search for more than one user:
python3 sherlock user1 user2 user3
Accounts found will be stored in an individual text file with the corresponding username (e.g user123.txt).
Video:
https://youtu.be/8bRyl-nm23M
[sc name=”ad-in-article”]



















whenever i try to clone. i get invaild syntax from python. i used two python 3.8 and python 3.6.4 and still no clue on how to clone plz help