Grouper is a slightly wobbly PowerShell module designed for pentesters and redteamers (although probably also useful for sysadmins) which sifts through the (usually very noisy) XML output from the Get-GPOReport cmdlet (part of Microsoft’s Group Policy module) and identifies all the settings defined in Group Policy Objects (GPOs) that might prove useful to someone trying to do something fun/evil.
Examples of the kinds of stuff it finds in GPOs:
- GPOs which grant modify permissions on the GPO itself to non-default users.
- Startup and shutdown scripts
- arguments and script themselves often include creds.
- scripts are often stored with permissions that allow you to modify them.
- MSI installers being automatically deployed
- again, often stored somewhere that will grant you modify permissions.
- Good old fashioned Group Policy Preferences passwords.
- Autologon registry entries containing credentials.
- Other creds being stored in the registry for fun stuff like VNC.
- Scheduled tasks with stored credentials.
- Also often run stuff from poorly secured file shares.
- User Rights
- Handy to spot where admins accidentally granted ‘Domain Users’ RDP access or those fun rights that let you run mimikatz even without full admin privs.
- Tweaks to local file permissions
- Good for finding those machines where the admins just stamped “Full Control” for “Everyone” on “C:\Program Files”.
- File Shares
- INI Files
- Environment Variables
- … and much more! (well, not very much, but some)
Note: While some function names might include the word audit, Groper is explicitly NOT meant to be an exhaustive audit for best practice configurations etc. If you want that, you should be using Microsoft SCT and LGPO.exe or something.
Usage
Generate a GPO Report on a Windows machine with the Group Policy cmdlets installed. These are installed on Domain Controllers by default, can be installed on Windows clients using RSAT, or can be enabled through the “Add Feature” wizard on Windows servers.
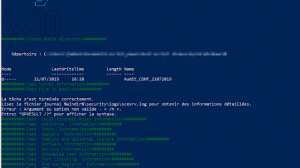
Get-GPOReport -All -ReportType xml -Path C:\temp\gporeport.xml
Import the Grouper module.
Import-Module grouper.ps1
Run Grouper.
Invoke-AuditGPOReport -Path C:\temp\gporeport.xml
Parameters
There’s also a couple of parameters you can mess with that alter which policy settings Grouper will show you:
-showDisabled
By default, Grouper will only show you GPOs that are currently enabled and linked to an OU in AD. This toggles that behaviour.
-Level
Grouper has 3 levels of filtering you can apply to its output.
- Show me all the settings you can.
- (Default) Show me only settings that seem ‘interesting’ but may or may not be vulnerable.
- Show me only settings that are definitely a super bad idea and will probably have creds in them or are going to otherwise grant me admin on a host.
Usage is straightforward. -Level 3, -Level 2, etc.


















Add Comment