Some quick tips if you use S3 buckets:
- Randomise your bucket names! There is no need to use
company-backup.s3.amazonaws.com. - Set appropriate permissions and audit regularly. If possible create two buckets – one for your public assets and another for private data.
- Be mindful about your data. What are suppliers, contractors and third parties doing with it? Where and how is it stored? These basic questions should be addressed in every info sec policy.
Installation
Python 3.4+ and pip3 are required. Then just:
git clone https://github.com/eth0izzle/bucket-stream.git- (optional) Create a virtualenv with
pip3 install virtualenv && virtualenv .virtualenv && source .virtualenv/bin/activate pip3 install -r requirements.txtpython3 bucket-stream.py
Usage
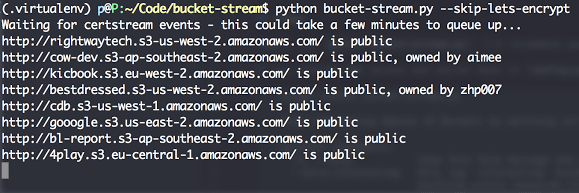
Simply run python3 bucket-stream.py.
If you provide AWS access and secret keys in config.yaml Bucket Stream will attempt to identity the buckets owner.
usage: python3 bucket-stream.py
Find interesting Amazon S3 Buckets by watching certificate transparency logs.
optional arguments:
-h, --help show this help message and exit
--only-interesting Only log 'interesting' buckets whose contents match
anything within keywords.txt (default: False)
--skip-lets-encrypt Skip certs (and thus listed domains) issued by Let's
Encrypt CA (default: False)
-t , --threads Number of threads to spawn. More threads = more power.
(default: 20)F.A.Qs
- Nothing appears to be happening
Patience! Sometimes certificate transparency logs can be quiet for a few minutes. - I found something highly confidential
Report it – please! You can usually figure out the owner from the bucket name or by doing some quick reconnaissance. Failing that contact Amazon’s support teams.


















Add Comment