BeRoot(s) is a post exploitation tool to check common Windows misconfigurations to find a way to escalate our privilege.
It will be added to the pupy project as a post exploitation module (so it will be executed in memory without touching the disk).
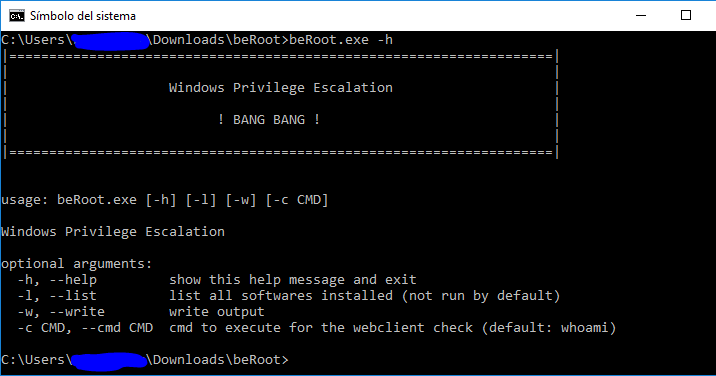
Run it
|====================================================================|
| |
| Windows Privilege Escalation |
| |
| ! BANG BANG ! |
| |
|====================================================================|usage: beRoot.exe [-h] [-l] [-w] [-c CMD]
Windows Privilege Escalation
optional arguments:
-h, –help show this help message and exit
-l, –list list all softwares installed (not run by default)
-w, –write write output
-c CMD, –cmd CMD cmd to execute for the webclient check (default: whoami)
All detection methods are described on the following document.
Path containing space without quotes
Consider the following file path:
C:Program FilesSome Testbinary.exe
If the path contains spaces and no quotes, Windows would try to locate and execute programs in the following order:
C:Program.exe
C:Program FilesSome.exe
C:Program FilesSome Folderbinary.exe
Following this example, if “C:” folder is writable, it would be possible to create a malicious executable binary called “Program.exe“. If “binary.exe” run with high privilege, it could be a good way to escalate our privilege.
Note: BeRoot realized these checks on every service path, scheduled tasks and startup keys located in HKLM.
How to exploit:
The vulnerable path runs as:
- a service: create a malicious service (or compile the service template)
- a classic executable: Create your own executable.
Consider the following file path:
C:Program FilesSome Testbinary.exe
If the root directory of “binary.exe” is writable (“C:Program FilesSome Test”) and run with high privilege, it could be used to elevate our privileges.
Note: BeRoot realized these checks on every service path, scheduled tasks and startup keys located in HKLM.
How to exploit:
- The service is not running:
- Replace the legitimate service by our own, restart it or check how it’s triggered (at reboot, when another process is started, etc.).
- The service is running and could not be stopped:
- Most exploitation will be like that, checks for dll hijacking and try to restart the service using previous technics.
This technic affects the following Windows version:
6.0 => Windows Vista / Windows Server 2008
6.1 => Windows 7 / Windows Server 2008 R2
6.2 => Windows 8 / Windows Server 2012
On a classic Windows installation, when DLLs are loaded by a binary, Windows would try to locate it using these following steps:
- Directory where the binary is located
- C:WindowsSystem32
- C:WindowsSystem
- C:Windows
- Current directory where the binary has been launched
- Directory present in %PATH% environment variable
If a directory on the %PATH% variable is writable, it would be possible to realize DLL hijacking attacks. Then, the goal would be to find a service which loads a DLL not present on each of these path. This is the case of the default “IKEEXT” service which loads the inexistant “wlbsctrl.dll“.
How to exploit: Create a malicious DLL called “wlbsctrl.dll” (use the DLL template) and add it to the writable path listed on the %PATH% variable. Start the service “IKEEXT“. To start the IKEEXT service without high privilege, a technic describe on the french magazine MISC 90 explains the following method:
Create a file as following:
C:UsersbobDesktop>type test.txt
[IKEEXTPOC]
MEDIA=rastapi
Port=VPN2-0
Device=Wan Miniport (IKEv2)
DEVICE=vpn
PhoneNumber=127.0.0.1
Use the “rasdial” binary to start the IKEEXT service. Even if the connection failed, the service should have been started.
C:UsersbobDesktop>rasdial IKEEXTPOC test test /PHONEBOOK:test.txt
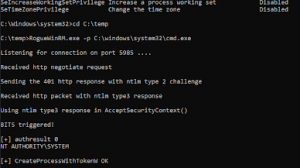
MS16-075
For French user, I recommend the article written on the MISC 90 which explain in details how it works.
This vulnerability has been corrected by Microsoft with MS16-075, however many servers are still vulnerable to this kind of attack. I have been inspired from the C++ POC available here
Here are some explaination (not in details):
- Start Webclient service (used to connect to some shares) using some magic tricks (using its UUID)
- Start an HTTP server locally
- Find a service which will be used to trigger a SYSTEM NTLM hash.
- Enable file tracing on this service modifying its registry key to point to our webserver (127.0.0.1@porttracing)
- Start this service
- Our HTTP Server start a negotiation to get the SYSTEM NTLM hash
- Use of this hash with SMB to execute our custom payload (SMBrelayx has been modify to realize this action)
- Clean everything (stop the service, clean the regritry, etc.).
How to exploit: BeRoot realize this exploitation, change the “-c” option to execute custom command on the vulnerable host.
beRoot.exe -c "net user Zapata LaLuchaSigue /add"
beRoot.exe -c "net localgroup Administrators Zapata /add"
AlwaysInstallElevated registry key
AlwaysInstallElevated is a setting that allows non-privileged users the ability to run Microsoft Windows Installer Package Files (MSI) with elevated (SYSTEM) permissions. To allow it, two registry entries have to be set to 1:
HKEY_CURRENT_USERSOFTWAREPoliciesMicrosoftWindowsInstallerAlwaysInstallElevated
HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsInstallerAlwaysInstallElevated
How to exploit: create a malicious msi binary and execute it.
Unattended Install files
This file contains all the configuration settings that were set during the installation process, some of which can include the configuration of local accounts including Administrator accounts. These files are available on these following path:
C:WindowsPantherUnattend.xml
C:WindowsPantherUnattended.xml
C:WindowsPantherUnattendUnattended.xml
C:WindowsPantherUnattendUnattend.xml
C:WindowsSystem32Sysprepunattend.xml
C:WindowsSystem32SysprepPantherunattend.xml
How to exploit: open the unattend.xml file to check if passwords are present on it. Should looks like:
<UserAccounts>
<LocalAccounts>
<LocalAccount>
<Password>
<Value>RmFrZVBhc3N3MHJk</Value>
<PlainText>false</PlainText>
</Password>
<Description>Local Administrator</Description>
<DisplayName>Administrator</DisplayName>
<Group>Administrators</Group>
<Name>Administrator</Name>
</LocalAccount>
</LocalAccounts>
</UserAccounts>
Other possible misconfigurations
Other tests are realized to check if it’s possible to:
- Modify an existing service
- Create a new service
- Modify a startup key (on HKLM)
- Modify directory where all scheduled tasks are stored: “C:Windowssystem32Tasks“




















Add Comment