WPScan is a free, for non-commercial use, black box WordPress vulnerability scanner written for security professionals and blog maintainers to test the security of their sites.
INSTALL
Prerequisites:
- Ruby >= 2.2.2 – Recommended: 2.3.3
- Curl >= 7.21 – Recommended: latest – FYI the 7.29 has a segfault
- RubyGems – Recommended: latest
From RubyGems:
gem install wpscanFrom sources:
Prerequisites: Git
git clone https://github.com/wpscanteam/wpscancd wpscan/
bundle install && rake installDocker
Pull the repo with docker pull wpscanteam/wpscan
Usage
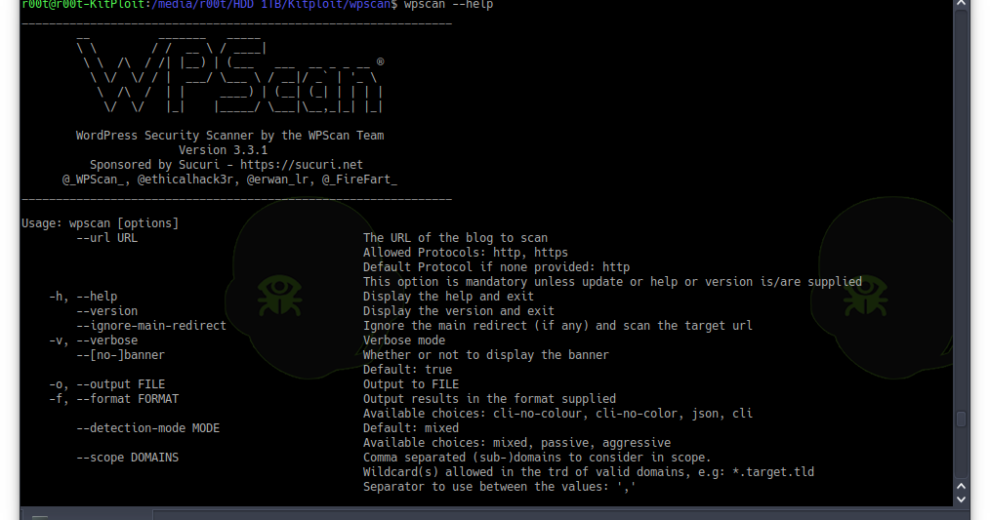
wpscan --url blog.tld This will scan the blog using default options with a good compromise between speed and accuracy. For example, the plugins will be checked passively but their version with a mixed detection mode (passively + aggressively). Potential config backup files will also be checked, along with other interesting findings. If a more stealthy approach is required, then wpscan --stealthy --url blog.tld can be used. As a result, when using the --enumerate option, don’t forget to set the --plugins-detection accordingly, as its default is ‘passive’.
For more options, open a terminal and type wpscan --help (if you built wpscan from the source, you should type the command outside of the git repo)
The DB is located at ~/.wpscan/db
WPScan can load all options (including the –url) from configuration files, the following locations are checked (order: first to last):
- ~/.wpscan/cli_options.json
- ~/.wpscan/cli_options.yml
- pwd/.wpscan/cli_options.json
- pwd/.wpscan/cli_options.yml
If those files exist, options from them will be loaded and overridden if found twice.
e.g:
~/.wpscan/cli_options.yml:
proxy: 'http://127.0.0.1:8080'
verbose: truepwd/.wpscan/cli_options.yml:
proxy: 'socks5://127.0.0.1:9090'
url: 'http://target.tld'Running wpscan in the current directory (pwd), is the same as wpscan -v --proxy socks5://127.0.0.1:9090 --url http://target.tld
PROJECT HOME
https://wpscan.org
VULNERABILITY DATABASE
https://wpvulndb.com



















Add Comment