[sc name=”ad_1″]
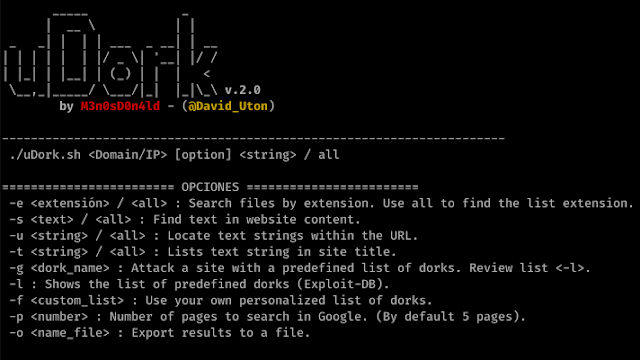
uDork is a script written in Bash Scripting that uses advanced Google search techniques to obtain sensitive information in files or directories, find IoT devices, detect versions of web applications, and so on.
uDork does NOT make attacks against any server, it only uses predefined dorks and/or official lists from exploit-db.com (Google Hacking Database: https://www.exploit-db.com/google-hacking-database).
New functional version: v.2.0
Author: M3n0sD0n4ld
Twitter: @David_Uton
Download and install:
$ git clone https://github.com/m3n0sd0n4ld/uDork
$ cd uDork
$ chmod +x uDork.sh
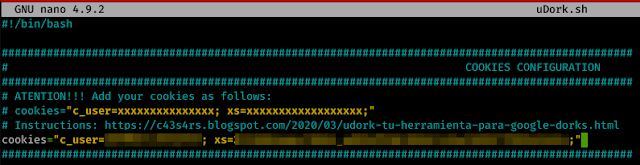
- Open the file "uDork.sh" and write inside this line:$ ./uDork.sh -hSteps to obtain the cookie and configure the cookie
- Login to facebook.com
- Now we will access www.messenger.com (It is the Facebook messaging app) and click on the “Continue as…” button.
- Once we’re in, all we have to do is get the two cookies we need to make uDork work.
3.1 – With firefox:
— Right mouse button and click on “Inspect”.
— Click on the “Network” tab and select any line that is in the domain “www.messenger.com“.
— Now click on the “Cookies” tab, copy and paste the cookies “c_user” and “xs” into the “uDork.sh” file.
Thus: cookies=”c_user=XXXXXX; xs=XXXXXX;”
3.2 – With Google Chrome
— Right mouse button and click on “Inspect”.
— Click on the tab “Application”, in the left column, look for the section “Cookies”, copy and paste the cookies “c_user” and “xs” with their value to the file “uDork.sh”.
Thus: cookies=”c_user=XXXXXX; xs=XXXXXX;”
Docker version:
Acknowledgement
Twitter: @interh4ck GitHub:(https://github.com/interhack86)
$ git clone https://github.com/m3n0sd0n4ld/uDork
$ cd uDork
$ docker build -t udork .
$ docker run --rm -it -e c_user=XXXXXXXXX -e xs=XXXXXXXXX udork -hUse:
Menu
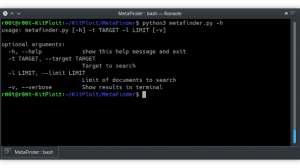
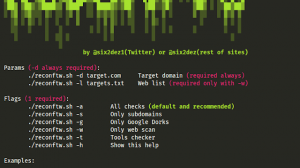
Example of searching pdf files
Example of a search for a list of default extensions.
Example of searching routes with the word “password”
Dorks listing
Example of use Dorks Massive
MORE RESULTS…
[sc name=”ad-in-article”]































Add Comment