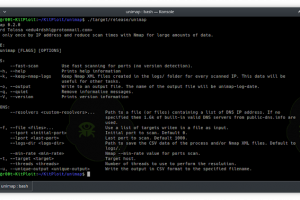
[sc name=”ad_1″] Scan only once by IP address and reduce scan times with Nmap for large amounts of data. Unimap is an abbreviation of “Unique...
Search Results For - Control
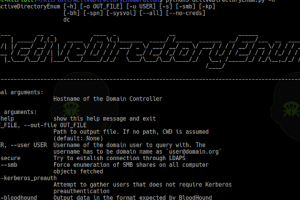
[sc name=”ad_1″] ADE – ActiveDirectoryEnum usage: activeDirectoryEnum [-h] [-o OUT_FILE] [-u USER] [-s] [-smb] [-kp] [-bh] [-spn] [--all] [...
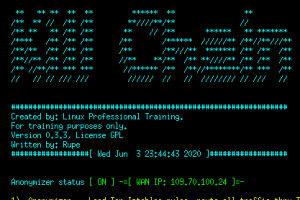
[sc name=”ad_1″] HTTP-revshell is a tool focused on redteam exercises and pentesters. This tool provides a reverse connection through the http/s...
[sc name=”ad_1″] For the most up-to-date information on Anchore Engine, Anchore CLI, and other Anchore software, please refer to the Anchore...
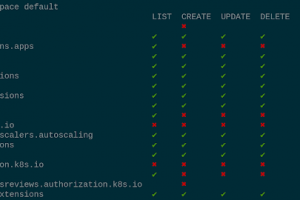
[sc name=”ad_1″] Review Access – kubectl plugin to show an access matrix for server resources Intro Have you ever wondered what access rights...
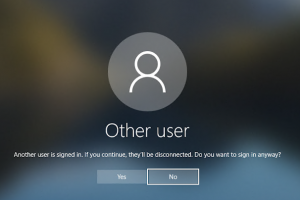
[sc name=”ad_1″] Pentest Cyber Range for a small Active Directory Domain. Automated templates for building your own Pentest/Red Team/Cyber Range in...
[sc name=”ad_1″] SNIcat is a proof of concept tool that performs data exfiltration, utilizing a covert channel method via. Server Name Indication...
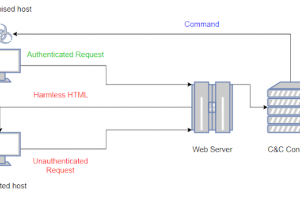
[sc name=”ad_1″] LOLBITS is a C2 framework that uses Microsoft’s Background Intelligent Transfer Service (BITS) to establish the...
[sc name=”ad_1″] What is “Kill Chain”? From Wikipedia: The term kill chain was originally used as a military concept related to the structure of an...
[sc name=”ad_1″] Did you ever wonder how you can move laterally through internal networks? or interact with remote machines without alerting EDRs...