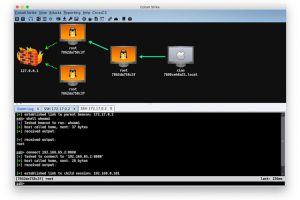
[sc name=”ad_1″] A security framework for enterprises and Red Team personnel, supports CobaltStrike’s penetration testing of other...
Search Results For - Configuration
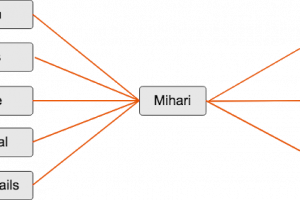
[sc name=”ad_1″] Mihari is a helper to run queries & manage results continuously. Mihari can be used for C2, landing page and phishing hunting...
[sc name=”ad_1″] Did you ever wonder how you can move laterally through internal networks? or interact with remote machines without alerting EDRs...
[sc name=”ad_1″] SecGen creates vulnerable virtual machines, lab environments, and hacking challenges, so students can learn security penetration...
[sc name=”ad_1″] Do you want to get threat intelligence data about a file, an IP or a domain? Do you want to get this kind of data from multiple...
[sc name=”ad_1″] Pyre is a performant type checker for Python compliant with PEP 484. Pyre can analyze codebases with millions of lines of code...
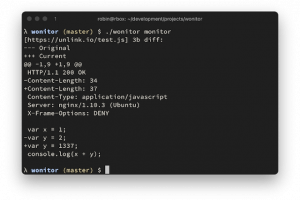
[sc name=”ad_1″] fast, zero config web endpoint change monitor. for comparing responses, a selected list of http headers and the full response body...
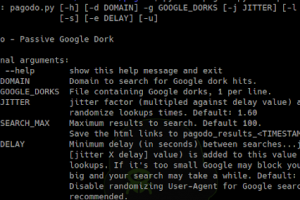
[sc name=”ad_1″] The goal of this project was to develop a passive Google dork script to collect potentially vulnerable web pages and applications...
[sc name=”ad_1″] Sinter is a 100% user-mode endpoint security agent for macOS 10.15 and above, written in Swift. Sinter uses the user-mode...
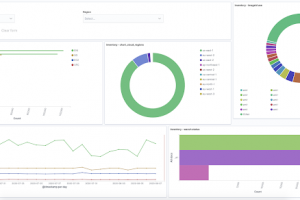
[sc name=”ad_1″] Dagobah is an open source tool written in python to automate the internal threat intelligence generation, inventory collection and...