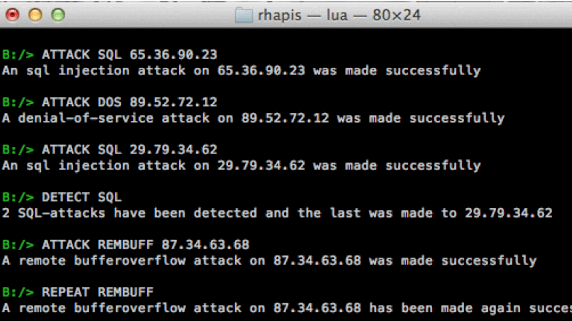
Network intrusion detection systems simulator. RHAPIS provides a simulation environment through which user is able to execute any IDS operation.
Basic Usage
Type HELP in the console in order to see the available commands. RHAPIS is written in Lua language. You need to have installed Lua in order to run RHAPIS.
The first commands that you must enter in order to install a virtual network intrusion detection system are the following:
SET NETIP1 [ip address], basic address of network in which NIDS is installed (network counters are 1-6).
SET HOSTIP1 [ip address], address of a host inside NIDS (host counters are 1-6).
INCLUDE config, loads a random configuration file
INCLUDE ruleset, reads a set of rules that will be identified by the intrusion detection system
Now you have activated detectability.
SET ATTHOSTIP1 [ip address]. With the current command you set an attacker’s identity. In this way, you will be able to make virtual attacks on random destinations by using the command ATTACK afterwards.
Host counters are again 1-6.
In order your attacks to be recognized by the intrusion detection system, you need to attack hosts that are part of the established network intrusion detection system.
For example:
SET HOSTIP1 7.7.7.7
ATTACK XSS 7.7.7.7
ATTACK XSS 9.9.9.9
DETECT XSSIn the above commands, the attack which will only be identified by NIDS will be that on destination address 7.7.7.7 because this is an active host of the network in which NIDS is installed.
On the other hand, the attack on 9.9.9.9 will not be detected.
Simulator Commands
ATTACK [type of attack] [destination IP address] = DOS,XSS,RFI,SQL,SHELL,REMBUFF,MALWARE,BRUTE,ARP,CSRF,MASQUERADE,PROBE,HIJACK
REPEAT [type of attack] = DOS,SHELL,REMBUFF,CSRF,SQL,XSS,ARP,RFI
GENERATE [type of traffic] [number of packets] = IN,OUT,MAL
SEND [type of packets] [number of packets] [destination IP address] = ACK,TCP,RST,FIN,MALF,UDP,SYN
INCLUDE ruleset,config
SET [network/hosts] [IP address] = NETIP1,NETIP2,NETIP3,NETIP4,NETIP5,HOSTIP1,HOSTIP2,HOSTIP3,HOSTIP4,HOSTIP5,HOSTIP6,ATTHOSTIP1,ATTHOSTIP2,ATTHOSTIP3,ATTHOSTIP4,ATTHOSTIP5,ATTHOSTIP6,ATTNETIP1,ATTNETIP2,ATTNETIP3,ATTNETIP4,ATTNETIP4,ATTNETIP5
HIDE/UNHIDE [undetectability] = MIX,DC
ATTEMPT [type of attack] [destination IP address] = DOS,XSS,LDAP,XPATH,SHELL
DETECT [type of attack] = DOS,XSS,RFI,SQL,SHELL,REMBUFF,MALWARE,BRUTE,ARP,CSRF,MASQUERADE,PROBE,HIJACK
ANALYZE [type of data] = HEX/FRAMES
The rest possible commands to be used are:
ALARMS, VISUALIZE, DATASET, INTRUDERS, HELP, INFO, ANONYMIZE
Examples
ATTACK DOS 7.7.7.7
ATTACK SHELL 2.2.2.2
GENERATE IN 660
DETECT SHELL
GENERATE MAL 1500
ATTACK MALWARE 5.5.5.5
DATASET
ATTEMPT XSS 10.10.10.10Inside the main directory you can find log files for every kind of information you enter on RHAPIS console (datasets, alarms, configuration, intruders, etc).


















Add Comment