[sc name=”ad_1″] Google’s one-year-old cybersecurity venture Chronicle today announced its first commercial product, called Backstory, a cloud-based...
[sc name=”ad_1″] Cybersecurity researcher at Google’s Project Zero division has publicly disclosed details and proof-of-concept exploit of a high...
[sc name=”ad_1″] Security researchers have finally, with “high confidence,” linked a previously discovered global cyber espionage campaign...
[sc name=”ad_1″] Coinhive, a notorious in-browser cryptocurrency mining service popular among cybercriminals, has announced that it will discontinue its...
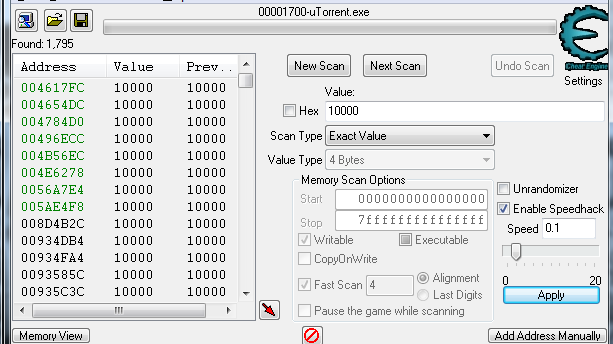
[sc name=”ad_1″] Cheat Engine is an open source tool designed to help you with modifying single player games running under window so you can make them harder...
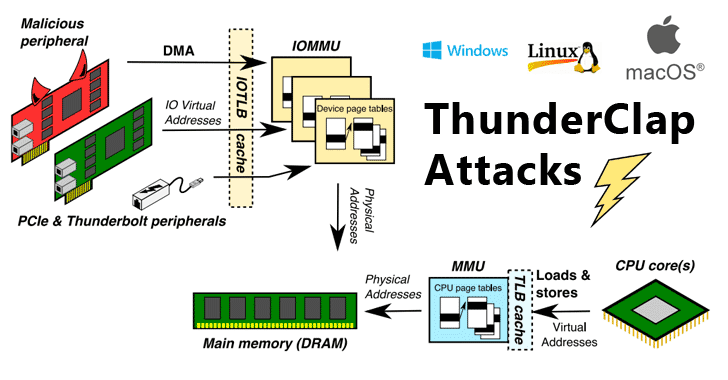
[sc name=”ad_1″] Security researchers have discovered a new class of security vulnerabilities that impacts all major operating systems, including Microsoft...
[sc name=”ad_1″] Security researchers have discovered two high-severity vulnerabilities in the SHAREit Android app that could allow attackers to bypass...
[sc name=”ad_1″] The world of cybersecurity is fast-paced and ever-changing. New attacks are unleashed every day, and companies around the world lose...
[sc name=”ad_1″] The Metasploit Project is a computer security project that provides information on vulnerabilities, helping in the development of...
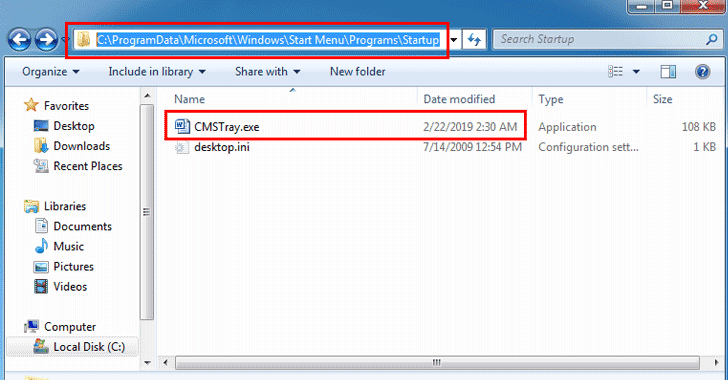
[sc name=”ad_1″] It’s not just the critical Drupal vulnerability that is being exploited by in the wild cybercriminals to attack vulnerable websites...