[sc name=”ad_1″] Pipe different tools with google dork Scanner Install zoid@MSI ~/dorkX> git clone zoid@MSI ~/dorkX> cd dorkX zoid@MSI...
[sc name=”ad_1″] Utility to find AES keys in running process memory. Works for 128, 192 and 256-bit keys. Usage Open aes-finder.sln solution in Visual Studio...
[sc name=”ad_1″] croc is a tool that allows any two computers to simply and securely transfer files and folders. AFAIK, croc is the only CLI file-transfer...
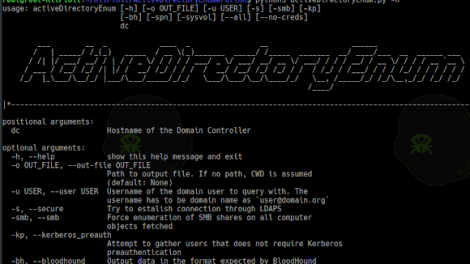
[sc name=”ad_1″] ADE – ActiveDirectoryEnum usage: activeDirectoryEnum [-h] [-o OUT_FILE] [-u USER] [-s] [-smb] [-kp] [-bh] [-spn] [--all] [--no-creds]...
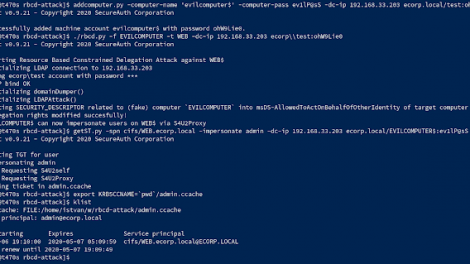
[sc name=”ad_1″] Abusing Kerberos Resource-Based Constrained Delegation TL;DR This repo is about a practical attack against Kerberos Resource-Based...
[sc name=”ad_1″] Chimera is a (shiny and very hack-ish) PowerShell obfuscation script designed to bypass AMSI and antivirus solutions. It digests malicious...
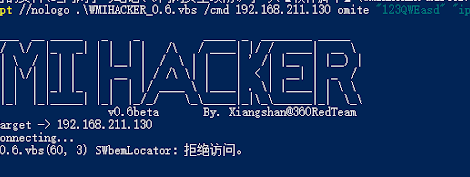
[sc name=”ad_1″] 中文版(Chinese version) Disclaimer: The technology involved in this project is only for security learning and defense purposes, illegal use is...
[sc name=”ad_1″] DockerENT is activE ruNtime application security scanning Tool (RAST tool) and framework which is pluggable and written in python. It comes...
[sc name=”ad_1″] HTTP-revshell is a tool focused on redteam exercises and pentesters. This tool provides a reverse connection through the http/s protocol. It...
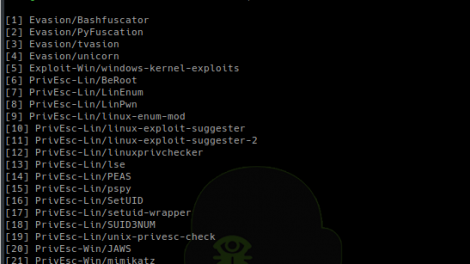
[sc name=”ad_1″] Some-Tools Why I was looking for a way to manage and keep up to date some tools that are not include in Kali-Linux. For exemple, I was...