Hey Guys, In this video i show you a great Security Auditing Tool for Unix/Linux Systems called Lynis. Lynis is an open source security auditing tool. Used by system...
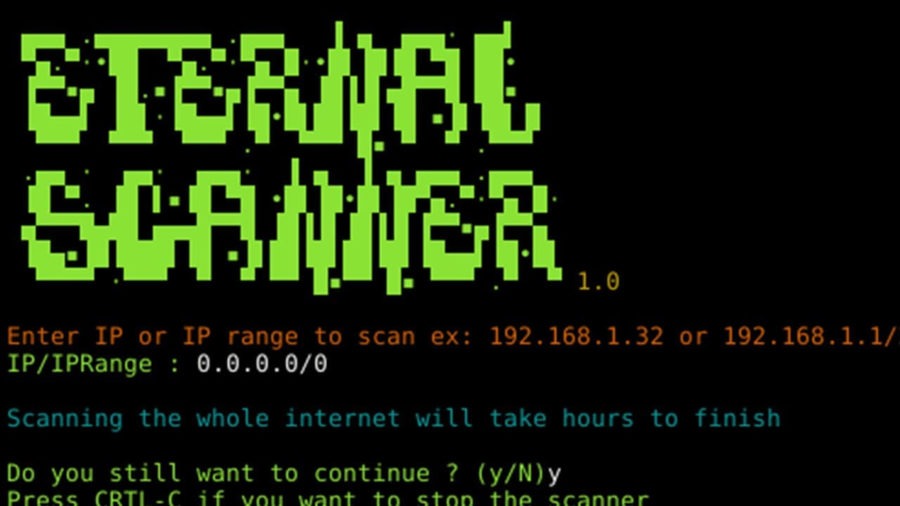
Eternal scanner is an network scanner for Eternal Blue exploit CVE-2017-0144 (Eternal Blue). Eternal Scanner: ; Requirements: • masscan • metasploit-framework Install...
Hey Guys, In this video i show you a fast and small SQL Injection Scanner. Damn Small SQLi Scanner (DSSS) is a fully functional SQL injection vulnerability scanner...
pythem is a multi-purpose pentest framework written in Python. It has been developed to be used by security researchers and security professionals. The tool intended to...
A python program to create a fake AP and sniff data new in 2.0: SSLstrip2 for HSTS bypass Image capture with Driftnet TShark for command line .pcap capture Features:...
Xerosploit is a penetration testing toolkit whose goal is to perform man in the middle attacks for penetration testing purposes. It brings various modules together that...
Sniffer is a C program that parses and interprets captured Ethernet traffic containing IP datagrams (UDP/TCP), and stores the captured payloads, email messages and HTTP...
Attack vectors There are 4 attack vectors available: beacon creds meterpreter meterpreter-grant For the ‘creds’ method, macphish can generate the Applescript script...
bettercap is a complete, modular, portable and easily extensible MITM tool and framework with every kind of diagnostic and offensive feature you could need in order to...
The objective of this program is to gather emails, subdomains, hosts, employee names, open ports and banners from different public sources like search engines, PGP key...