cve-search is a tool to import CVE (Common Vulnerabilities and Exposures) and CPE (Common Platform Enumeration) into a MongoDB to facilitate search and processing of...
Are you a proud iPhone owner? If yes, this could freak you up. Trust me! Your iPhone has a serious privacy concern that allows iOS app developers to take your...
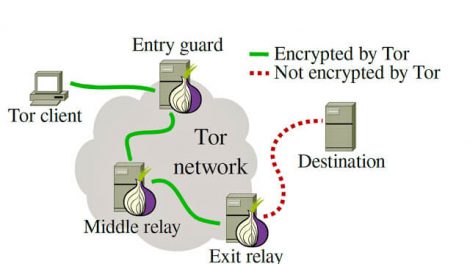
Use nmap to scan hidden “onion” services on the Tor network. Minimal image based on alpine, using proxychains to wrap nmap. Tor and dnsmasq are run as daemons via s6...
Canvas fingerprinting relies on websites meaning able to receive data from HTML canvas details calmly. In future, Firefox users will be required to give their approval...
“I don’t remember if my data has been sold to the dark web or where this goes,” she said. “I keep getting letters from Kohl’s, from Macy’s, from Old Navy saying, ‘Thank...
Yet another disgusting human being has been arrested and charged for assaulting a child and posting proof on the Dark Web. The Traunstein, Germany man, 28, has been...
Onion Routed Cloud is a decentralized, anonymous, object storage platform owned and operated by allies in defense of human rights and opposition to censorship. ORC is a...
Across the Internet, hundreds of thousands of sites rely on Google’s reCaptcha system for defense against bots (in fact, Devpost uses reCaptcha when creating a new...
Tweep is an advanced Twitter scraping tool written in python that allows for scraping Tweets and pictures from Twitter profiles without using Twitter’s API...
Exitmap is a fast and modular Python-based scanner for Tor exit relays. Exitmap modules implement tasks that are run over (a subset of) all exit relays. If you have a...