Hey Guys, In this video i show you how to perform Wi-Fi deauthentication attack on any Wi-Fi Network. Wi-Fi deauthentication attack is a type of denial-of-service attack...
Parat is a simple remote administration tool(RAT) written in python. Features Fully UnDetectable(FUD) Compatible with Telegram messanger Bypass windows User Account...
p0wnedShell is an offensive PowerShell host application written in C# that does not rely on powershell.exe but runs powershell commands and functions within a powershell...
This is Part 2 of Linux Basics In this Part we will talk about your first steps with linux. Logging In and Out: The Linux system distinguishes between different users...
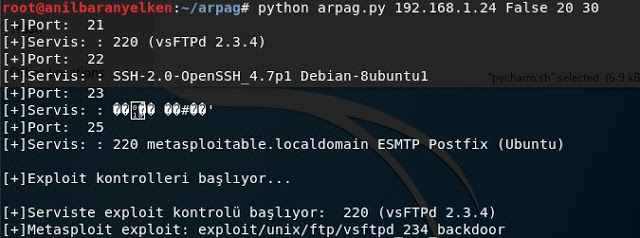
arpa?: In Turkish mythology magical word means. The tool name arpag has been selected because it has made the exploit process automatic. Installation: git clone cd...
[sc name=”ad_1″] Hey Guys, In this video i show you how to Embed a Metasploit Payload in an Original .Apk File. Normally we have to install the payload in...
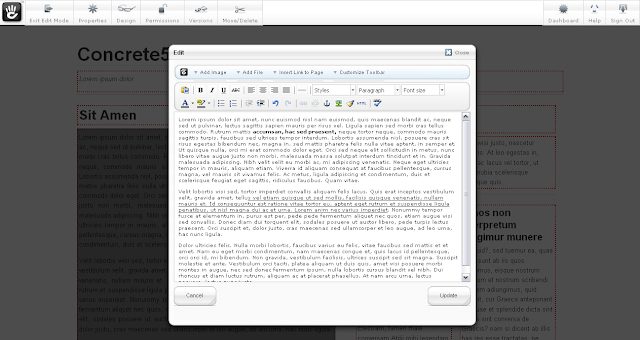
Vulnerability scanner and information gatherer for the Concrete5 CMS. Is a little out of date presently pending a refactor. concrete5 is an open-source content...
This will be the beggining of a long series of the basics of linux, so let’s get started. What is Linux? Open-Source? What is the use of Linux? Linux is an...
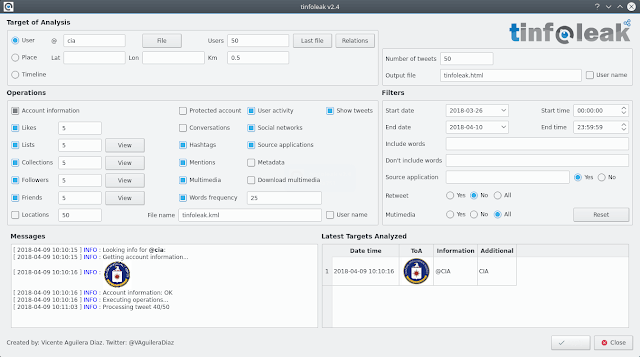
The most complete open-source tool for Twitter intelligence analysis Introduction tinfoleak is an open-source tool within the OSINT (Open Source Intelligence) and...
CloudFrunt is a tool for identifying misconfigured CloudFront domains. CloudFront is a Content Delivery Network (CDN) provided by Amazon Web Services (AWS). CloudFront...