[sc name=”ad_1″]
Oblivion is a tool focused in real time monitoring of new data leaks, notifying if the credentials of the user has been leak out. It’s possible too verify if any credential of user has been leak out before. The Oblivion have two modes:
- Oblivion Client: graphical mode.
- Oblivion Server: mode with API functionalities.
NOTE: The Oblivion Client and the Oblivion Server are independents.
Oblivion Client
Oblivion Server
Oblivion Features
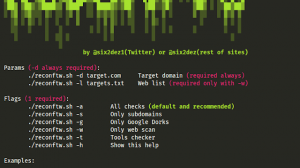
- CVEs scan
- Works with powerful APIs
- Works too with Google Dorks
- Checks your password in Word Lists
- Checks the last pastes in Pastebin
- Output to txt, docx, pdf, xlsx, json, html, xml, db
- Output to encrypted files
- Sends result files to multiples Buckets S3
- Upload the result files to Google Drive
- Cab send result files by SSH (work with EC2)
- Notify by Telegram and e-mail
- Includes option to hide passwords for demonstrations
- Works with scheduled scans
- Possible to execute loop scans
APIs
| Service | Functions | Status |
|---|---|---|
| HaveIBeenPwned | E-mails and passwords | paid |
| Scylla.sh | Cleartext passwords, hashs and salts, usernames, IPs, domain | free |
| IntelX.io | Cleartext passwords, hashs and salts, usernames, IPs, domain, Bitcoin Wallets, IBAN | paid |
| Circl.lu | Checks for new CVEs | free |
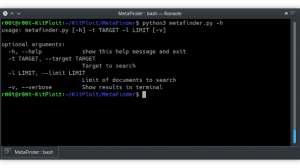
Usage and configuration
For configuration or usage of Oblivion please read the documentation. All the steps were careful explained with images and examples.
Thanks and credits
- Peter Kleissner and the Intelligence X team
- Alejandro Caceres (Scylla)
- khast3x
- Daniel Miessler
- Gustavo Melgaço
- Alberico de Castro
- Eliabe Kaique
[sc name=”ad-in-article”]





















Add Comment