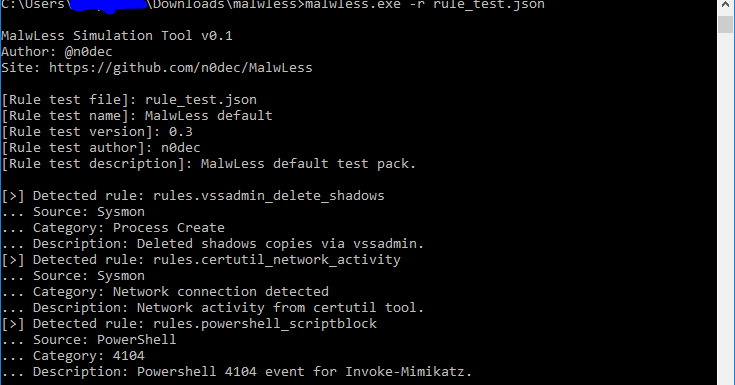
MalwLess is an open source tool that allows you to simulate system compromise or attack behaviours without running processes or PoCs. The tool is designed to test Blue Team detections and SIEM correlation rules. It provides a framework based on rules that anyone can write, so when a new technique or attack comes out you can write your own rules and share it a with the community.MalwLess can parse the rules and write them directly to the Windows EventLog, then you can foward it to your event collector.MalwLess Simulation Tool v1.1
Author: @n0dec
Site: https://github.com/n0dec/MalwLess[Rule test file]: rule_test.json
[Rule test name]: MalwLess default
[Rule test version]: 0.3
[Rule test author]: n0dec
[Rule test description]: MalwLess default test pack.
[>] Detected rule: rules.vssadmin_delete_shadows
... Source: Sysmon
... Category: Process Create
... Description: Deleted shadows copies via vssadmin.
[>] Detected rule: rules.certutil_network_activity
... Source: Sysmon
... Category: Network connection detected
... Description: Network activity from certutil tool.
[>] Detected rule: rules.powershell_scriptblock
... Source: PowerShell
... Category: 4104
... Description: Powershell 4104 event for Invoke-Mimikatz.
Releases
You can download the latest release on https://github.com/n0dec/MalwLess/releases
Requirements
It is necessary to have sysmon installed in your system. https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon
Commands
When you have downloaded the latest release version you can run it directly from an elevated command prompt.
To test the default rule set which is on rule_test.json just download it and run:
> malwless.exe If you want to test a different rule set file, use the -r parameter:
> malwless.exe -r your_pack.json To write a custom rule set check the writing sets section.
Creating rules
Anyone can create a rule. These are written in json with an easy format.
| key | values |
|---|---|
enabled |
If the value is set to true the event will be written. If it’s set to false just ignore the rule. |
source |
The source of the events. (Working on more supported sources…)SysmonPowerShell |
category |
For each source there are a list of different categories that can be specified. |
description |
A simple rule description. |
payload |
These are the values that will be added to the event. If you don’t indicate a specific payload the event will contain the values of the default configuration files located on conf. |
Rule example
> malwless.exeSets
Awesome gists sets- Windows oneliners
windows-oneliners.jsonref: https://arno0x0x.wordpress.com/2017/11/20/windows-oneliners-to-download-remote-payload-and-execute-arbitrary-code/ APTSimulator setref: https://github.com/NextronSystems/APTSimulatorEndgame RTA setref: https://github.com/endgameinc/RTAWinPwnage setref: https://github.com/rootm0s/WinPwnage
Contact
For any issue or suggestions contact on twitter @n0dec.



















Add Comment