Easy-to-use live forensics toolbox for Linux endpoints written in Python & Flask.
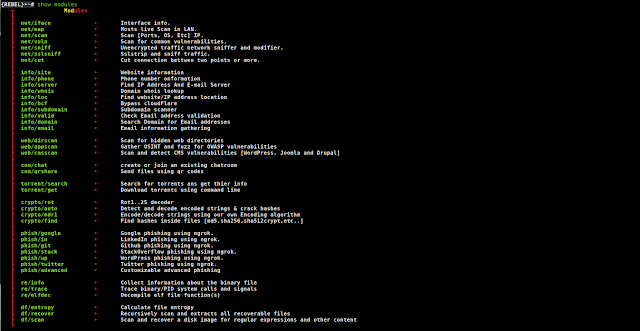
Capabilities
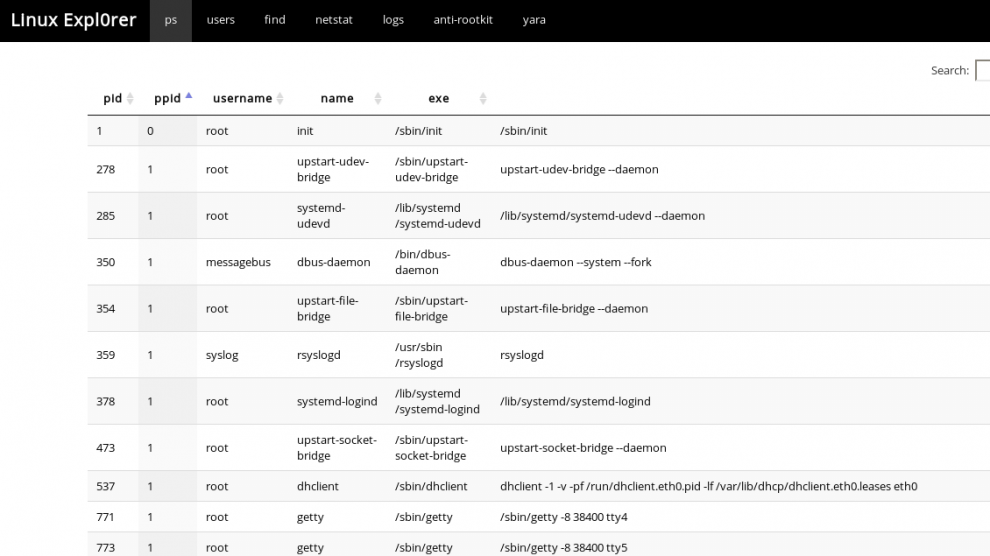
ps
- View full process list
- Inspect process memory map & fetch memory strings easly
- Dump process memory in one click
- Automaticly search hash in public services
users
- users list
find
- Search for suspicious files by name/regex
netstat
- Whois
logs
- syslog
- auth.log(user authentication log)
- ufw.log(firewall log)
- bash history
anti-rootkit
- chkrootkit
yara
- Scan a file or directory using YARA signatures by @Neo23x0
- Scan a running process memory address space
- Upload your own YARA signature
Requirements
- Python 2.7
- YARA
- chkrootkit
Installation
- Clone repository
- Install required packages
pip install -r requirements.txt- Setup VT/OTX api keys
nano config.pyEdit following lines:
VT_APIKEY = '<key>'
OTX_APIKEY = '<key>'- Install YARA
sudo apt-get install yara- Install chkrootkit
sudo apt-get install chkrootkitStart Linux Expl0rer server
sudo python linux_explorer.pyUsage
- Start your browser
firefox http://127.0.0.1:8080- do stuff
Notes
- We recommend using NGINX reverse proxy with basic http auth & ssl for secure remote access
- Tested with Ubuntu 16.04

















Add Comment