Modern applications leverage the availability of existing components for use as building blocks in application development. By using existing components, organizations can dramatically decrease time-to-market. Reusing existing components however, comes at a cost. Organizations that build on top of existing components assume risk for software they did not create. Vulnerabilities in third-party components are inherited by all applications that use those components. The OWASP Top Ten (2013 and 2017) both recognize the risk of using components with known vulnerabilities.
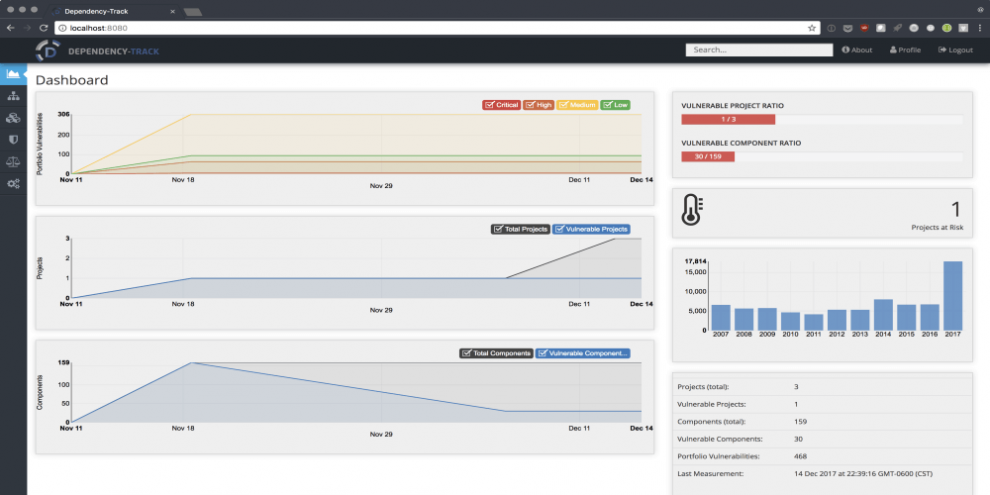
Dependency-Track is a Software Composition Analysis (SCA) platform that keeps track of all third-party components used in all the applications an organization creates or consumes. It integrates with multiple vulnerability databases including the National Vulnerability Database (NVD), Node Security Platform (NSP), and VulnDB from Risk Based Security. Dependency-Track monitors all applications in its portfolio in order to proactively identify vulnerabilities in components that are placing your applications at risk. Use of Dependency-Track can play a vital role in an overall Supply Chain Risk Management (SCRM) program by providing many of the recommendations outlined in the NIST Cybersecurity Framework.
Dependency-Track is designed to be used in an automated DevOps environment where Dependency-Check results or specific BOM (Bill of Material) formats are automatically ingested during CI/CD. Use of the Dependency-Check Jenkins Plugin is highly recommended for this purpose and is well suited for use in Jenkins Pipeline. In such an environment, Dependency-Track enables your DevOps teams to accelerate while still keeping tabs on component usage and any inherited risk.
Dependency-Track can also be used to monitor vulnerabilities in COTS (commercial off-the-shelf) software.
NOTICE: Dependency-Track is beta-quality software. v3 will launch in March.
Features
- Dramatically increases visibility into the use of vulnerable components
- Supports an unlimited number of projects and components
- Projects can range from applications, operating systems, firmware, to IoT devices
- Tracks vulnerabilities across entire project portfolio
- Tracks vulnerabilities by component
- Easily identify projects that are potentially vulnerable to newly published vulnerabilities
- Supports standardized SPDX license ID’s and tracks license use by component
- Supports CycloneDX and SPDX bill-of-material formats
- Easy to read metrics for components, projects, and portfolio
- API-first design facilitates easy integration with other systems
- API documentation available in Swagger 2.0 (OpenAPI 3 support coming soon)
- Flexible authentication supports internally managed users, Active Directory/LDAP, and API Keys
- Simple to install and configure. Get up and running in just a few minutes

- Dependency-Check results can be published to SonarQube (plugin)
- Dependency-Check results can be published to ThreadFix (plugin)
- Dependency-Check results can be published to Dependency-Track
- Software bill-of-materials can be published to Dependency-Track
- Dependency-Check can use Dependency-Track as a source of evidence
- Dependency-Track results can be integrated into ThreadFix



















Add Comment