Bashark aids pentesters and security researchers during the post-exploitation phase of security audits.
Usage
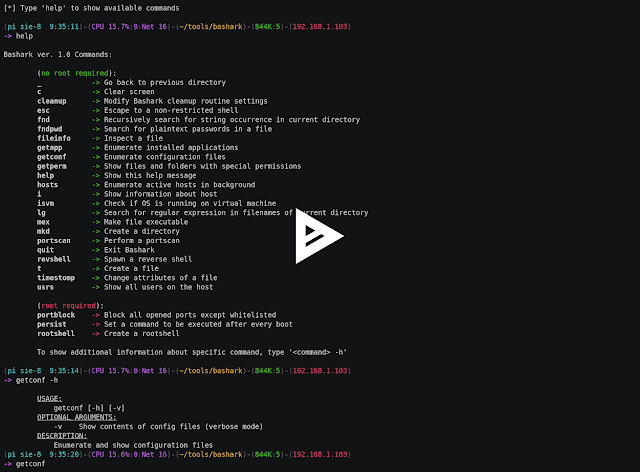
To launch Bashark on compromised host, simply source the bashark.sh script from terminal: $ source bashark.sh Then type help to see Bashark’s help menu
Features
- Single Bash script
- Lightweight and fast
- Multi-platform: Unix, OSX, Solaris etc.
- No external dependencies
- Immune to heuristic and behavioural analysis
- Built-in aliases of often used shell commands
- Extends system shell with post-exploitation oriented functionalities
- Stealthy, with custom cleanup routine activated on exit
- Easily extensible (add new commands by creating Bash functions)
- Full tab completion
Demo





















Add Comment