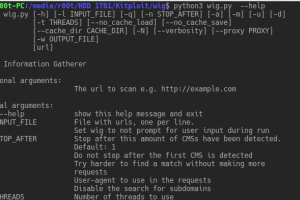
wig is a web application information gathering tool, which can identify numerous Content Management Systems and other administrative applications. The...
Search Results For - Information
Striker is an offensive information and vulnerability scanner. Features Just supply a domain name to Striker and it will automatically do the following for...
It’s a pretty simple trade model, actually. They assume as much data about you from lenders, aggregate it, and sell it back to them,” said Brett Horn, an...
[sc name=”ad_1″] WordPress user enumeration and login Brute Force tool for Windows and Linux With the Brute Force tool, you can control how...
[sc name=”ad_1″] CDK is an open-sourced container penetration toolkit, designed for offering stable exploitation in different slimmed containers...
[sc name=”ad_1″] HosTaGe is a lightweight, low-interaction, portable, and generic honeypot for mobile devices that aims on the detection of...
[sc name=”ad_1″] BigBountyRecon tool utilises 58 different techniques using various Google dorks and open source tools to expedite the process of...
[sc name=”ad_1″] Collect OSINT for GitLab groups and members and search the group and group members’ snippets, issues, and issue discussions...
[sc name=”ad_1″] This cli is for pentesters, CTF players, or dev. You can modify your jwt, sign, inject ,etc… Check Documentation for more...
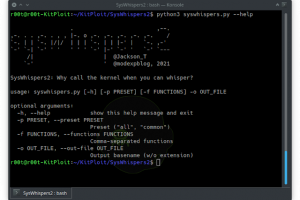
[sc name=”ad_1″] SysWhispers helps with evasion by generating header/ASM files implants can use to make direct system calls. All core syscalls are...