[sc name=”ad_1″] Ransomware written in NodeJs. Install and run git clone cd nodeCrypto && npm install You must edit first variable in index...
Search Results For - Configuration
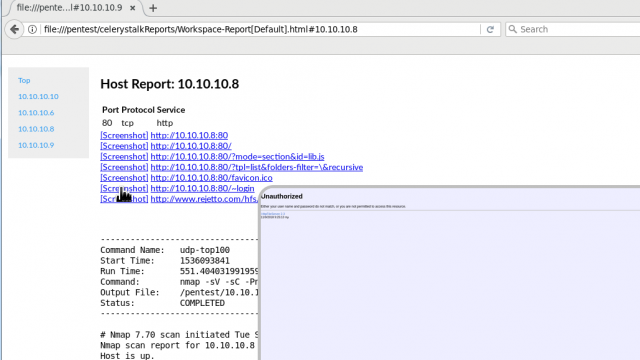
[sc name=”ad_1″] celerystalk helps you automate your network scanning/enumeration process with asynchronous jobs (aka tasks) while retaining full...
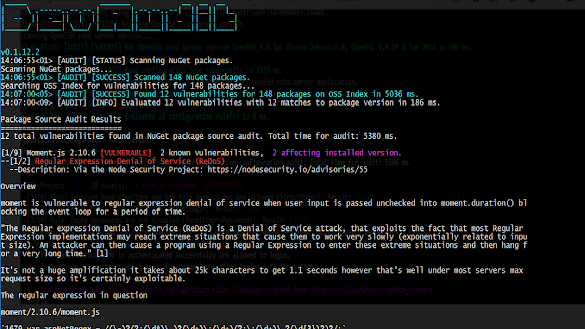
[sc name=”ad_1″] DevAudit is an open-source, cross-platform, multi-purpose security auditing tool targeted at developers and teams adopting DevOps...
[sc name=”ad_1″] An RTSP stream access tool that comes with its library Cameradar allows you to Detect open RTSP hosts on any accessible target...
[sc name=”ad_1″] dawnscanner is a source code scanner designed to review your ruby code for security issues. dawnscanner is able to scan plain ruby...
[sc name=”ad_1″] Developers of phpMyAdmin, one of the most popular and widely used MySQL database management systems, today released an updated...
Looking for an automated malware analysis software? Something like a 1-click solution that doesn’t require any installation or configuration…a...
ACHE is a focused web crawler. It collects web pages that satisfy some specific criteria, e.g., pages that belong to a given domain or that contain a user...
Pacu is an open source AWS exploitation framework, designed for offensive security testing against cloud environments. Created and maintained by Rhino Security...
novahot is a webshell framework for penetration testers. It implements a JSON-based API that can communicate with trojans written in any language. By default...