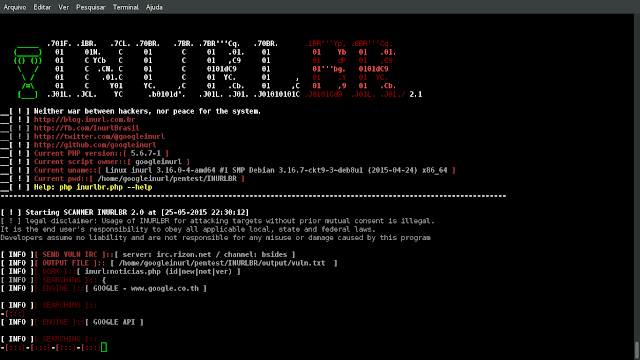
Advanced search in search engines, enables analysis provided to exploit GET / POST capturing emails & urls, with an internal custom validation junction for each...
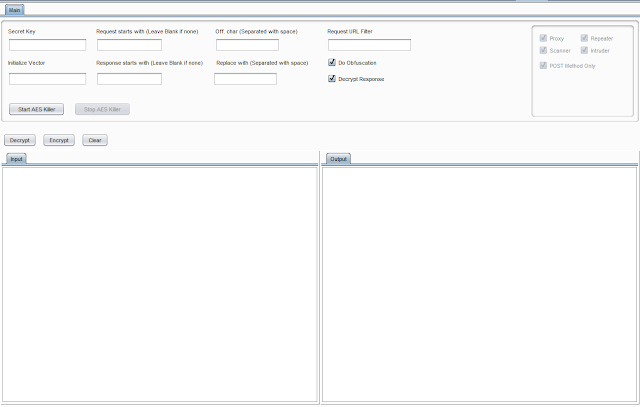
Burpsuite Plugin to decrypt AES Encrypted traffic on the fly. Requirements Burpsuite Java Tested on Burpsuite 1.7.36 Windows 10 xubuntu 18.04 Kali Linux 2018 What it...
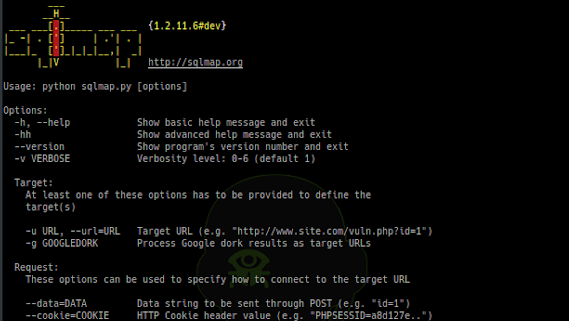
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It...
Armor is a simple Bash script designed to create encrypted macOS payloads capable of evading antivirus scanners. Below is an example gif of Armor being used with a...
Scannerl is a modular distributed fingerprinting engine implemented by Kudelski Security. Scannerl can fingerprint thousands of targets on a single host, but can just as...
Parrot 4.3 is now available for download. This release provides security and stability updates and is the starting point for the plan to develop an LTS edition of Parrot...
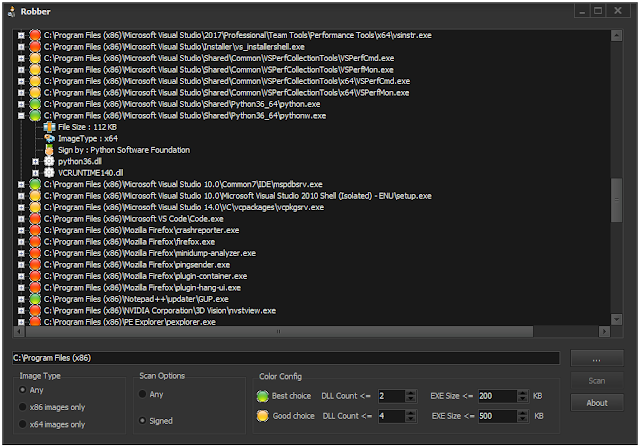
Robber is a free open source tool developed using Delphi XE2 without any 3rd party dependencies. What is DLL hijacking ?! Windows has a search path for DLLs in its...
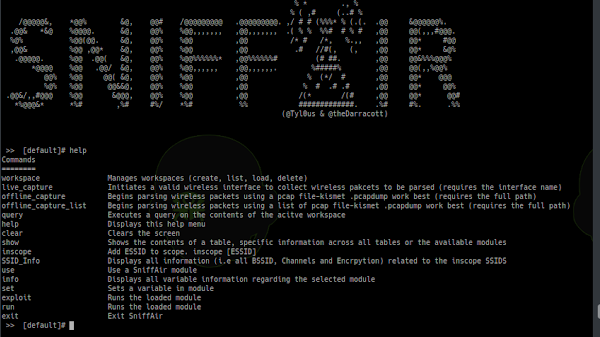
SniffAir is an open-source wireless security framework which provides the ability to easily parse passively collected wireless data as well as launch sophisticated...
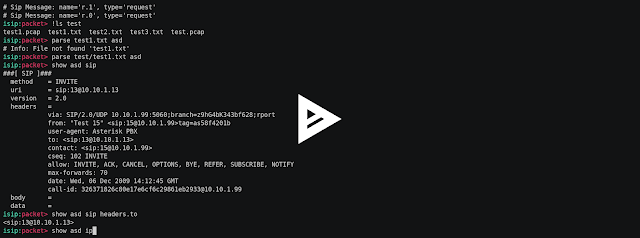
Interactive sip toolkit for packet manipulations, sniffing, man in the middle attacks, fuzzing, simulating of dos attacks. Video Setup git clone cd isip pip install -r...
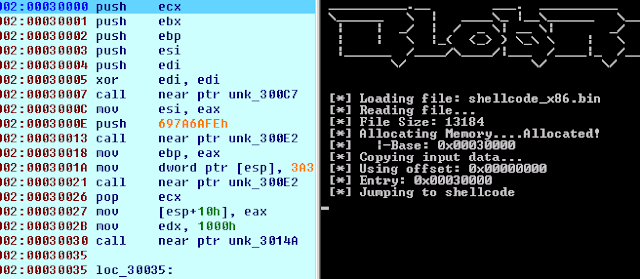
BlobRunner is a simple tool to quickly debug shellcode extracted during malware analysis. BlobRunner allocates memory for the target file and jumps to the base (or...