theHarvester is a tool for gathering subdomain names, e-mail addresses, virtual hosts, open ports/ banners, and employee names from different public sources (search...
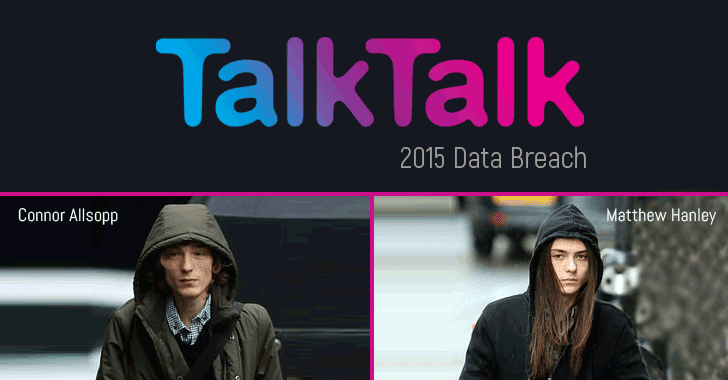
[sc name=”ad_1″] Two hackers have been sent to prison for their roles in hacking TalkTalk, one of the biggest UK-based telecommunications company, in 2015...
[sc name=”ad_1″] It seems as though not a day goes by without a new story breaking about a high-level cyber attack on a major corporation or national...
[sc name=”ad_1″] This is why you should always think twice before opening innocent looking email attachments, especially word and pdf files. Cybersecurity...
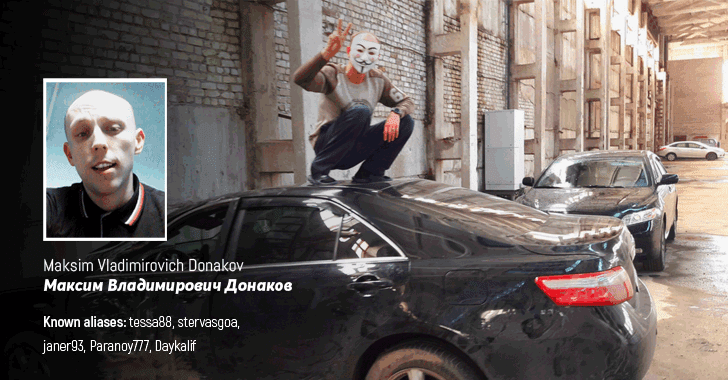
[sc name=”ad_1″] The real identity of Tessa88—the notorious hacker tied to several high-profile cyber attacks including the LinkedIn, DropBox and MySpace...
[sc name=”ad_1″] Here we have great news for all bug bounty hunters. Now you can get paid up to $40,000 for finding and responsibly reporting critical...
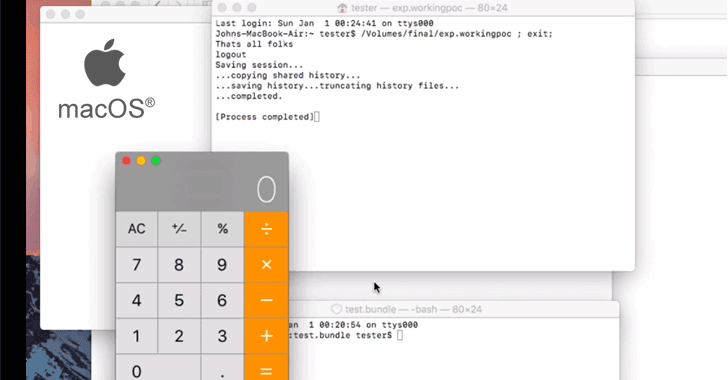
[sc name=”ad_1″] Earlier this week Dropbox team unveiled details of three critical vulnerabilities in Apple macOS operating system, which altogether could...
[sc name=”ad_1″] The United States Postal Service has patched a critical security vulnerability that exposed the data of more than 60 million customers to...
[sc name=”ad_1″] A widely used third-party NodeJS module with nearly 2 million downloads a week was compromised after one of its open-source contributor gone...
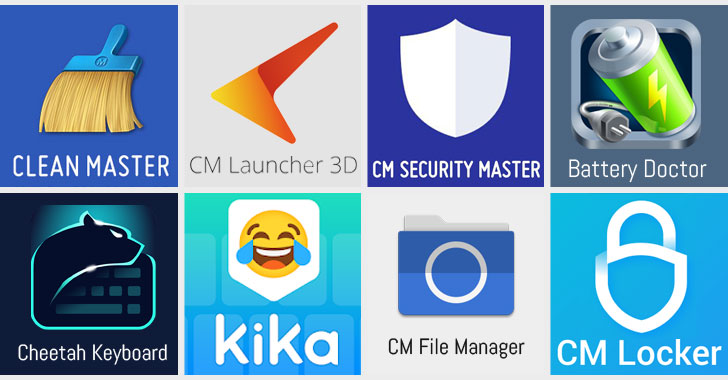
[sc name=”ad_1″] Cheetah Mobile—a prominent Chinese app company, known for its popular utility apps like Clean Master and Battery Doctor—and one of its...