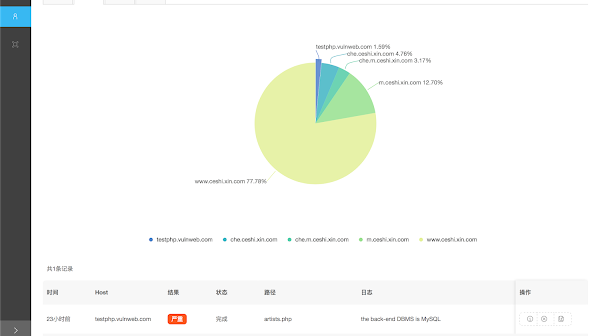
[sc name=”ad_1″] Automatic SQL injection with Charles and sqlmapapi Dependencies Django PostgreSQL Celery sqlmap redis Supported platforms Linux osx...
[sc name=”ad_1″] Doppelganger is a python script to scan duplicate copies in a given directory. This tool compare not only file names, but also file hashes...
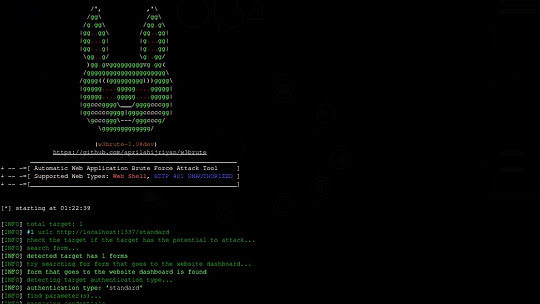
w3brute is an open source penetration testing tool that automates attacks directly to the website’s login page. w3brute is also supported for carrying out brute...
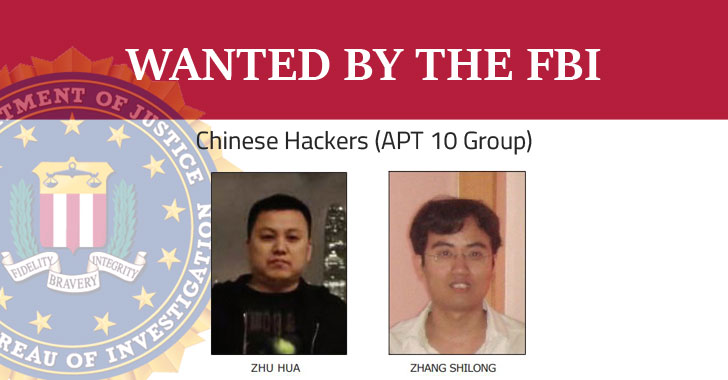
[sc name=”ad_1″] The US Department of Justice on Thursday charged two Chinese hackers associated with the Chinese government for hacking numerous companies...
[sc name=”ad_1″] The FBI just saved the Christmas. The U.S. Justice Department announced earlier today that the FBI has seized domains of 15 “DDoS-for...
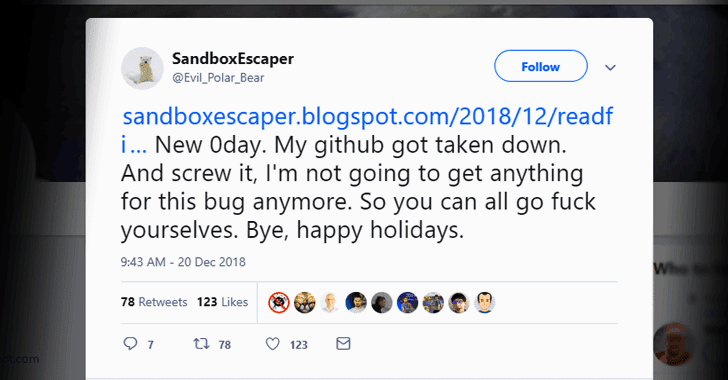
[sc name=”ad_1″] A security researcher with Twitter alias SandboxEscaper today released proof-of-concept (PoC) exploit for a new zero-day vulnerability...
[sc name=”ad_1″] Microsoft today issued an out-of-band security update to patch a critical zero-day vulnerability in Internet Explorer (IE) Web browser that...
[sc name=”ad_1″] Another day, another data breach. This time it’s the United States National Aeronautics and Space Administration (NASA) NASA today...
[sc name=”ad_1″] Security researchers have discovered yet another example of how cybercriminals disguise their malware activities as regular traffic by using...
[sc name=”ad_1″] Twitter has been hit with a minor data breach incident that the social networking site believes linked to a suspected state-sponsored attack...