[sc name=”ad_1″] A simple DDoS attack could land you in jail for 10 years or even more. A Massachusetts man has been sentenced to over 10 years in prison for...
[sc name=”ad_1″] Almost every activity on the Internet starts with a DNS query, a key function of the Internet that works as an Internet’s directory...
[sc name=”ad_1″] Security researchers have discovered three vulnerabilities in Systemd, a popular init system and service manager for most Linux operating...
[sc name=”ad_1″] Cybersecurity researcher has discovered online a massive database containing records of more than 202 million Chinese citizens that remained...
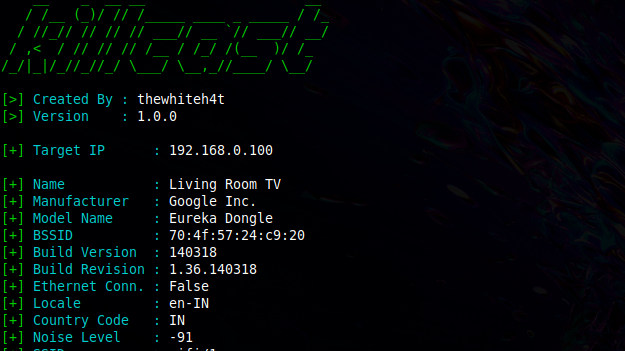
[sc name=”ad_1″] Manipulate Chromecast Devices in your Network. Inspiration – Thousands of Google Chromecast Devices Hijacked to Promote PewDiePie This...
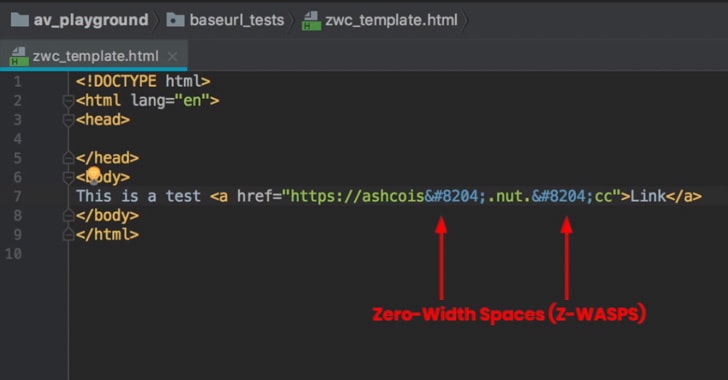
[sc name=”ad_1″] Security researchers have been warning about a simple technique that cybercriminals and email scammers are already being using in the wild...
[sc name=”ad_1″] Microsoft has issued its first Patch Tuesday for this year to address 49 CVE-listed security vulnerabilities in its Windows operating...
[sc name=”ad_1″] Google has removed 85 apps from its Play Store after finding out that they were pushing aggressive, full-screen adware to Android users...
[sc name=”ad_1″] German police are seeking your help in gathering information related to a MAC address that could lead to the cell phone device used by a DHL...
[sc name=”ad_1″] Popular cryptocurrency exchange Coinbase has suspended all transactions of Ethereum Classic (ETC)—the original unforked version of the...