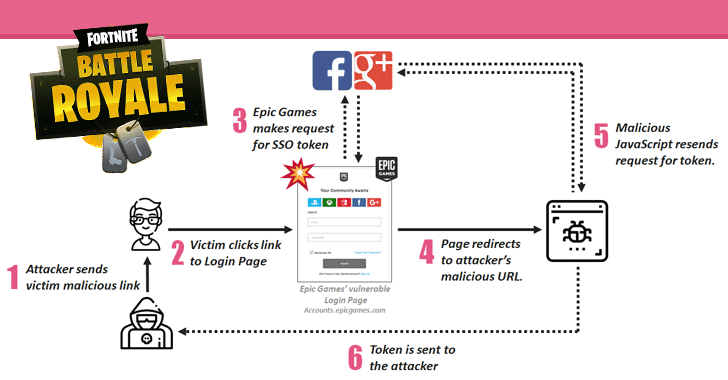
[sc name=”ad_1″] Check Point researchers have discovered multiple security vulnerabilities in Fortnite, a massively popular online battle game, one of which...
[sc name=”ad_1″] A set of 36-year-old vulnerabilities has been uncovered in the Secure Copy Protocol (SCP) implementation of many client applications that...
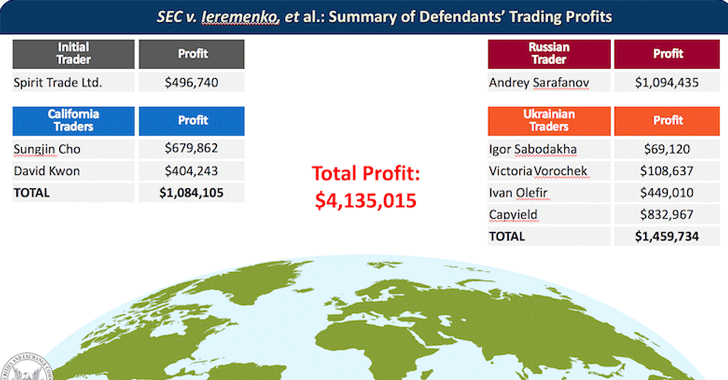
[sc name=”ad_1″] The U.S. authorities have charged two Ukrainian hackers for hacking into the Securities and Exchange Commission’s EDGAR filing system...
[sc name=”ad_1″] A new reminder for those who are still holding on to the Windows 7 operating system—you have one year left until Microsoft ends support for...
[sc name=”ad_1″] A zero-day vulnerability has been discovered and reported in the Microsoft’s Windows operating system that, under a certain scenario...
[sc name=”ad_1″] If you are responsible for the cybersecurity of a medium-sized company, you may assume your organization is too small to be targeted. Well...
[sc name=”ad_1″] Good news, the new Kickass Torrents site is back. Back in July 2017, popular BitTorrent site Kickass Torrents (KAT cr) was taken down by the...
[sc name=”ad_1″] Remember “The Shadow Brokers” and the arrest of a former NSA contractor accused of stealing 50 Terabytes of top secret documents...
[sc name=”ad_1″] If your computer has been infected with PyLocky Ransomware and you are searching for a free ransomware decryption tool to unlock or decrypt...
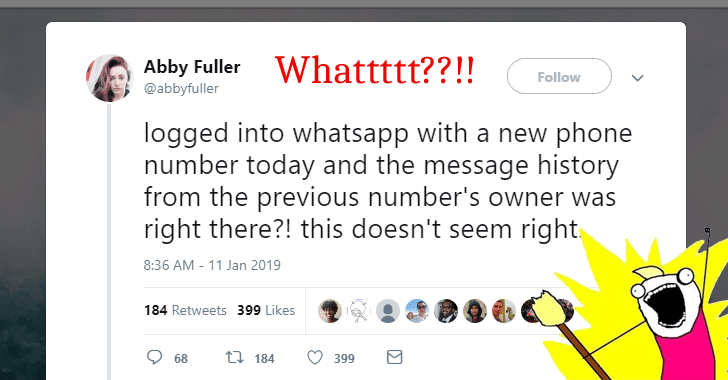
[sc name=”ad_1″] In-short conclusion—Whatsapp service or its 45-days deletion policy doesn’t seem to have a bug. For detailed logical explanation...